Introduction
Access Control Management Software is used to control who can enter physical locations, digital systems, or secured areas within an organization. These platforms help businesses enforce security policies by managing identities, permissions, authentication, and real-time access monitoring.
In modern security ecosystems, access control software is a core part of physical security + cybersecurity convergence, often integrated with CCTV, biometrics, and identity management systems. It is widely used in enterprises, government buildings, hospitals, data centers, and smart facilities.
Common use cases:
- Employee door access management
- Visitor and contractor access control
- Multi-site facility security
- Identity-based access permissions
- Real-time access monitoring and audit logs
Key evaluation criteria:
- Role-based access control (RBAC)
- Multi-factor authentication (MFA) support
- Real-time monitoring and alerts
- Integration with CCTV and security systems
- Cloud vs on-prem deployment options
- Scalability for enterprise environments
- Compliance and audit reporting
- Ease of administration and usability
Best for: Enterprises, IT security teams, government buildings, hospitals, universities, and large facilities.
Not ideal for: Small personal setups without structured security or identity management needs.
Key Trends in Access Control Management Software
- Shift toward cloud-based access control platforms
- Adoption of Zero Trust security architecture
- Increased use of mobile credentials instead of physical cards
- Integration with biometric authentication systems
- Expansion of AI-based access anomaly detection
- Unified platforms combining physical + digital access control
- Strong focus on identity governance and compliance automation
- API-first access control ecosystems
- Real-time access analytics and reporting dashboards
- Integration with HR and workforce systems
How We Selected These Tools (Methodology)
- Evaluated global enterprise adoption and usage
- Reviewed identity and access management capabilities
- Assessed physical security integration features
- Considered scalability across multi-location enterprises
- Included both cloud-native and legacy enterprise systems
- Analyzed security compliance and audit capabilities
- Focused on real-world access control deployments
- Balanced IAM platforms and physical access control systems
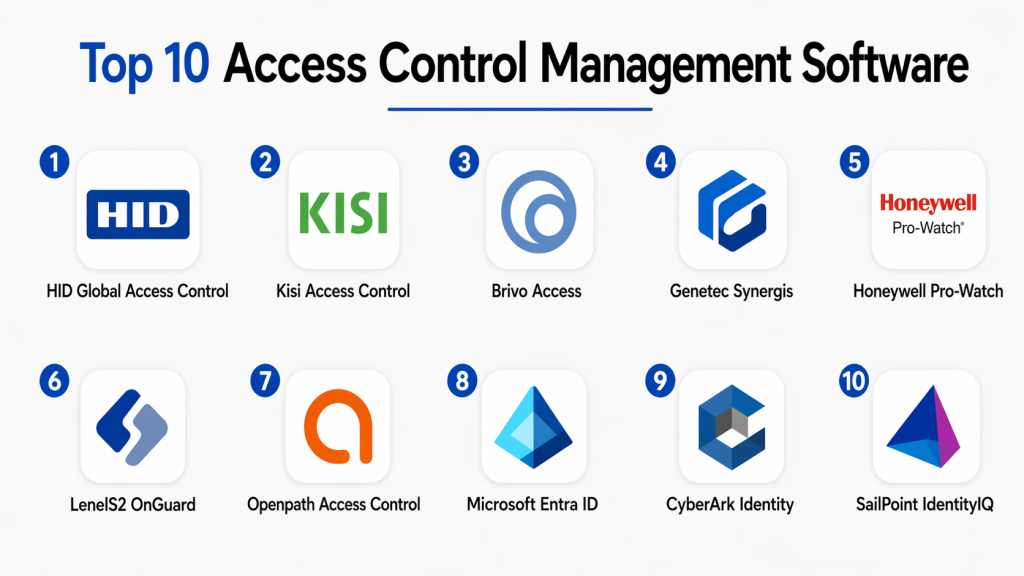
Top 10 Access Control Management Software
#1 — HID Global Access Control
Short description: A widely used enterprise access control platform that provides secure identity-based physical access management with strong hardware and software integration for large organizations.
Key Features
- Identity-based access control
- Smart card and biometric support
- Role-based permissions
- Real-time access monitoring
- Secure credential management
Pros
- Strong enterprise adoption
- Highly secure ecosystem
Cons
- Complex setup
- Hardware dependency
Platforms / Deployment
Cloud / On-prem / Hybrid
Security & Compliance
Enterprise-grade encryption and authentication
Integrations & Ecosystem
Works with HID readers, biometrics, and security systems
Support & Community
Strong global enterprise support
#2 — Kisi Access Control
Short description: A cloud-based access control platform designed for modern workplaces with mobile credentials and remote door management.
Key Features
- Mobile access credentials
- Remote door unlocking
- Cloud-based management
- Audit logs and reporting
- Multi-site control
Pros
- Easy deployment
- Modern mobile-first design
Cons
- Requires stable internet
- Subscription-based
Platforms / Deployment
Cloud / Mobile
Security & Compliance
Encrypted cloud access control
Integrations & Ecosystem
Supports smart locks and third-party security systems
Support & Community
Strong SMB + enterprise support
#3 — Brivo Access
Short description: A cloud-native access control system offering centralized security management with advanced analytics and integrations.
Key Features
- Cloud-based access control
- Mobile credentials
- Real-time monitoring
- API integrations
- Security analytics
Pros
- Highly scalable
- Strong cloud architecture
Cons
- Subscription cost
- Hardware requirements
Platforms / Deployment
Cloud
Security & Compliance
Enterprise security compliance
Integrations & Ecosystem
Works with surveillance and HR systems
Support & Community
Strong enterprise support
#4 — Genetec Synergis
Short description: A unified security platform combining access control, video surveillance, and identity management for large-scale enterprise environments.
Key Features
- Unified security dashboard
- Access + video integration
- Role-based access control
- Incident management
- Multi-site scalability
Pros
- All-in-one security platform
- Highly reliable
Cons
- Expensive
- Complex deployment
Platforms / Deployment
Cloud / Hybrid / On-prem
Security & Compliance
High-level enterprise compliance
Integrations & Ecosystem
Works with Genetec security ecosystem
Support & Community
Enterprise-grade support
#5 — Honeywell Pro-Watch
Short description: An enterprise access control system designed for high-security environments such as government and critical infrastructure.
Key Features
- Centralized access management
- Multi-layer authentication
- Alarm integration
- Audit trail reporting
- Scalable architecture
Pros
- Strong security focus
- Industrial-grade reliability
Cons
- Complex UI
- High cost
Platforms / Deployment
On-prem / Hybrid
Security & Compliance
Enterprise security compliance
Integrations & Ecosystem
Works with Honeywell security systems
Support & Community
Strong enterprise support
#6 — LenelS2 OnGuard
Short description: A widely used enterprise access control platform for managing physical security in large organizations.
Key Features
- Role-based access control
- Visitor management
- Real-time monitoring
- Alarm integration
- Audit logging
Pros
- Highly scalable
- Strong enterprise reliability
Cons
- Complex setup
- Expensive licensing
Platforms / Deployment
On-prem / Hybrid
Security & Compliance
Enterprise-grade security
Integrations & Ecosystem
Works with surveillance and identity systems
Support & Community
Strong global enterprise support
#7 — Openpath Access Control
Short description: A mobile-first access control system designed for modern workplaces with touchless entry and cloud management.
Key Features
- Mobile credential access
- Touchless entry
- Cloud management
- Real-time alerts
- Visitor access control
Pros
- Modern UI
- Easy deployment
Cons
- Subscription pricing
- Internet dependency
Platforms / Deployment
Cloud
Security & Compliance
Encrypted cloud access
Integrations & Ecosystem
Works with smart locks and enterprise systems
Support & Community
Strong SMB adoption
#8 — Microsoft Entra ID
Short description: A cloud identity and access management platform that controls digital access across enterprise applications and systems.
Key Features
- Identity and access management
- Single sign-on (SSO)
- Conditional access policies
- MFA authentication
- Identity governance
Pros
- Strong enterprise ecosystem
- Deep Microsoft integration
Cons
- Complex configuration
- Enterprise-focused
Platforms / Deployment
Cloud
Security & Compliance
Enterprise-grade Microsoft security
Integrations & Ecosystem
Works with Microsoft 365 and Azure
Support & Community
Strong global enterprise support
#9 — CyberArk Identity
Short description: A privileged access management and identity security platform focused on securing enterprise systems and sensitive accounts.
Key Features
- Privileged access control
- SSO and MFA
- Identity lifecycle management
- Session monitoring
- Risk-based authentication
Pros
- Strong security focus
- Enterprise-grade protection
Cons
- Complex deployment
- High cost
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
High-level enterprise security
Integrations & Ecosystem
Works with enterprise IT systems
Support & Community
Strong enterprise support
#10 — SailPoint IdentityIQ
Short description: An identity governance platform that manages access permissions, compliance, and identity lifecycle across enterprise systems.
Key Features
- Identity governance
- Access certification
- Role-based access control
- Compliance reporting
- Lifecycle management
Pros
- Strong compliance tools
- Enterprise scalability
Cons
- Complex setup
- High cost
Platforms / Deployment
Cloud / On-prem
Security & Compliance
Strong compliance support
Integrations & Ecosystem
Works with enterprise applications
Support & Community
Strong enterprise ecosystem
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| HID Global | Physical access control | Multi-platform | Hybrid | Secure identity control | N/A |
| Kisi | Smart offices | Cloud/Mobile | Cloud | Mobile access | N/A |
| Brivo | Cloud access control | Web | Cloud | API-first system | N/A |
| Genetec Synergis | Enterprise security | Multi-platform | Hybrid | Unified security | N/A |
| Honeywell Pro-Watch | Critical infrastructure | Multi-platform | On-prem | High security | N/A |
| LenelS2 OnGuard | Large enterprises | Multi-platform | Hybrid | Scalable control | N/A |
| Openpath | Modern workplaces | Cloud/Mobile | Cloud | Touchless access | N/A |
| Microsoft Entra | Digital identity | Cloud | Cloud | SSO + IAM | N/A |
| CyberArk Identity | Privileged access | Multi-platform | Hybrid | Zero Trust security | N/A |
| SailPoint IdentityIQ | Identity governance | Multi-platform | Hybrid | Compliance automation | N/A |
Evaluation & Scoring of Access Control Tools
| Tool Name | Core | Ease | Integrations | Security | Performance | Support | Value | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| HID Global | 10 | 7 | 9 | 10 | 9 | 9 | 7 | 8.7 |
| Kisi | 8 | 9 | 8 | 8 | 8 | 8 | 9 | 8.3 |
| Brivo | 9 | 8 | 9 | 9 | 9 | 9 | 8 | 8.7 |
| Genetec | 10 | 7 | 10 | 10 | 9 | 9 | 7 | 8.8 |
| Honeywell | 9 | 7 | 8 | 10 | 9 | 9 | 7 | 8.4 |
| LenelS2 | 9 | 7 | 8 | 9 | 9 | 9 | 7 | 8.3 |
| Openpath | 8 | 9 | 8 | 8 | 8 | 8 | 8 | 8.2 |
| Microsoft Entra | 9 | 8 | 10 | 10 | 9 | 9 | 9 | 9.0 |
| CyberArk | 9 | 7 | 9 | 10 | 9 | 9 | 7 | 8.6 |
| SailPoint | 9 | 7 | 9 | 10 | 9 | 9 | 7 | 8.6 |
Frequently Asked Questions (FAQs)
1. What is access control management software?
It is a system used to manage who can access physical or digital resources in an organization. It controls permissions, authentication, and entry logs.
2. Why is access control important?
It helps protect sensitive areas, data, and assets by ensuring only authorized users can gain access, reducing security risks.
3. What industries use access control systems?
Industries like banking, healthcare, government, IT, manufacturing, and education widely use access control systems.
4. What is the difference between IAM and physical access control?
IAM manages digital system access, while physical access control manages entry to buildings and secure physical spaces.
5. Are access control systems cloud-based?
Many modern systems are cloud-based, but enterprise solutions also support hybrid and on-prem deployments.
6. Can access control integrate with CCTV?
Yes, most systems integrate with surveillance cameras for real-time monitoring and incident tracking.
7. What authentication methods are used?
Common methods include passwords, smart cards, biometrics, mobile credentials, and MFA.
8. Are access control systems secure?
Yes, they use encryption, authentication protocols, and audit logs to ensure security.
9. Can I control access remotely?
Yes, cloud-based systems allow remote access management through mobile apps or dashboards.
10. What is the best access control software?
Microsoft Entra, Genetec, HID Global, and Brivo are among the top enterprise solutions depending on use case.
Conclusion
Access Control Management Software plays a critical role in securing both physical and digital environments. It enables organizations to enforce strict security policies, monitor access in real time, and maintain compliance with industry regulations. There is no single best solution for everyone. Enterprises often choose Genetec or HID Global for physical security, while Microsoft Entra and SailPoint dominate digital identity management. Cloud-first organizations prefer Brivo, Kisi, or Openpath. The right choice depends on your security requirements, infrastructure, and scalability needs. Focus on integration, ease of management, and long-term security strategy. Start by evaluating a few platforms, testing integration with your systems, and choosing a solution that aligns with your organization’s security architecture.