Introduction
Cloud Workload Protection Platforms (CWPP) are security solutions designed to protect workloads—such as virtual machines, containers, and serverless applications—across cloud, hybrid, and multi-cloud environments. These platforms provide continuous monitoring, threat detection, vulnerability assessment, and runtime protection to secure applications as they run in the cloud.
As organizations rapidly adopt cloud-native architectures, workloads become more dynamic and distributed, increasing the risk of attacks. Traditional security tools are often insufficient because they lack real-time visibility into workload behavior. CWPP tools address this by offering centralized visibility, automated security controls, and runtime threat protection across diverse environments.
Common Use Cases
- Protecting virtual machines, containers, and serverless workloads
- Detecting runtime threats such as malware and ransomware
- Monitoring workload behavior and anomalies
- Securing DevOps pipelines and cloud-native applications
- Ensuring compliance across cloud environments
What Buyers Should Evaluate
- Coverage across workloads (VMs, containers, serverless)
- Runtime protection and threat detection capabilities
- Agent-based vs agentless architecture
- Integration with DevOps and cloud platforms
- Automation and response capabilities
- Compliance and reporting features
- Scalability across multi-cloud environments
- Ease of deployment and management
- Cost vs value
Best for: Security teams, DevSecOps engineers, cloud architects, and enterprises operating multi-cloud or containerized environments.
Not ideal for: Organizations without cloud workloads or those requiring only basic infrastructure-level security.
Key Trends in CWPP Tools
- Shift toward CNAPP (unifying CSPM + CWPP)
- AI-driven threat detection and anomaly analysis
- Agentless + agent-based hybrid models
- Deep runtime visibility using eBPF and behavioral analytics
- Integration with DevSecOps pipelines
- Focus on container and Kubernetes security
- Real-time attack detection and response
- Identity-based security controls and zero-trust models
- API-first architecture for automation
- Expansion into attack path analysis and exposure management
How We Selected These Tools (Methodology)
- Strong industry adoption and credibility
- Proven runtime protection capabilities
- Comprehensive multi-cloud support
- Integration with cloud and DevOps ecosystems
- Availability of automation and response features
- Suitability for different organization sizes
- Balance of enterprise and modern cloud-native tools
- Strong documentation and support ecosystems
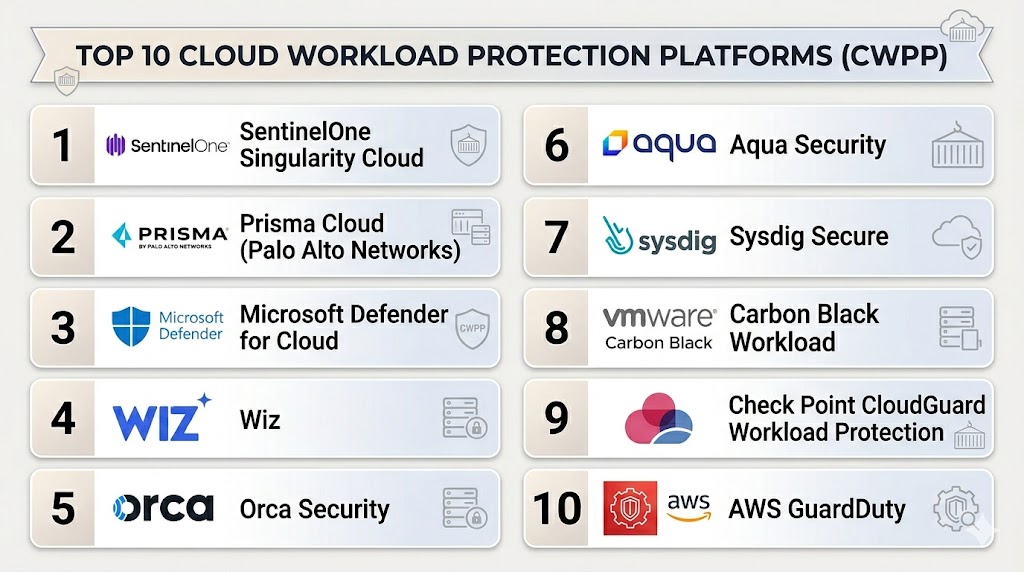
Top 10 Cloud Workload Protection Platforms (CWPP)
#1 — SentinelOne Singularity Cloud
Short description: An AI-driven platform providing real-time protection for cloud workloads across containers, VMs, and serverless environments.
Key Features
- AI-powered threat detection
- Runtime protection
- Behavioral analytics
- Automated response
- Multi-cloud support
- Forensic visibility
Pros
- Strong AI-driven automation
- Deep runtime visibility
Cons
- Premium pricing
- Requires tuning
Platforms / Deployment
- Cloud
Security & Compliance
- RBAC, encryption
- Compliance support varies
Integrations & Ecosystem
- Cloud providers
- SIEM tools
- APIs
- DevOps tools
Support & Community
Enterprise support and documentation.
#2 — Prisma Cloud (Palo Alto Networks)
Short description: A comprehensive cloud security platform combining CWPP with broader cloud-native protection.
Key Features
- Workload protection
- Container security
- Compliance monitoring
- Threat detection
- DevOps integration
- Risk prioritization
Pros
- Full-stack security
- Strong enterprise capabilities
Cons
- Complex deployment
- Higher cost
Platforms / Deployment
- Cloud
Security & Compliance
- RBAC, encryption
- Compliance frameworks supported
Integrations & Ecosystem
- Cloud platforms
- APIs
- DevOps tools
Support & Community
Enterprise-grade support.
#3 — Microsoft Defender for Cloud
Short description: A cloud-native security platform offering integrated workload protection and posture management.
Key Features
- Multi-cloud workload protection
- Threat detection
- Compliance monitoring
- Risk assessment
- Integration with Microsoft ecosystem
Pros
- Strong ecosystem integration
- Easy deployment
Cons
- Best for Microsoft environments
- Limited outside ecosystem
Platforms / Deployment
- Cloud
Security & Compliance
- SSO, MFA, RBAC
- Compliance support varies
Integrations & Ecosystem
- Azure services
- Microsoft tools
- APIs
Support & Community
Strong enterprise support.
#4 — Wiz
Short description: A modern cloud security platform offering agentless workload visibility and risk analysis.
Key Features
- Agentless scanning
- Risk prioritization
- Attack path analysis
- Cloud visibility
- Compliance monitoring
Pros
- Easy deployment
- Strong visualization
Cons
- Premium pricing
- Limited manual control
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Cloud providers
- DevOps tools
- APIs
Support & Community
Strong enterprise support.
#5 — Orca Security
Short description: An agentless CWPP platform focused on deep visibility and security insights across cloud workloads.
Key Features
- Agentless workload scanning
- Risk prioritization
- Vulnerability detection
- Compliance checks
- Full-stack visibility
Pros
- No agent overhead
- Deep insights
Cons
- Premium pricing
- Requires tuning
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Cloud platforms
- APIs
Support & Community
Enterprise support.
#6 — Aqua Security
Short description: A cloud-native security platform specializing in container and Kubernetes workload protection.
Key Features
- Container security
- Runtime protection
- Vulnerability scanning
- Compliance monitoring
- DevSecOps integration
Pros
- Strong container focus
- DevOps-friendly
Cons
- Complex setup
- Requires expertise
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Kubernetes
- CI/CD tools
- APIs
Support & Community
Strong support and documentation.
#7 — Sysdig Secure
Short description: A runtime security platform focused on containerized workloads and Kubernetes environments.
Key Features
- Runtime threat detection
- Kubernetes security
- Compliance monitoring
- Risk prioritization
- DevOps integration
Pros
- Strong container security
- Real-time monitoring
Cons
- Requires Kubernetes expertise
- Learning curve
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Kubernetes
- APIs
- DevOps tools
Support & Community
Good documentation and support.
#8 — VMware Carbon Black Workload
Short description: A cloud workload security solution focused on endpoint and workload protection.
Key Features
- Endpoint protection
- Workload security
- Threat detection
- Behavioral analytics
- Risk assessment
Pros
- Strong endpoint integration
- Enterprise-ready
Cons
- Complex setup
- Higher cost
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- VMware ecosystem
- APIs
Support & Community
Enterprise support.
#9 — Check Point CloudGuard Workload Protection
Short description: A cloud security platform offering workload protection and compliance management.
Key Features
- Workload protection
- Compliance monitoring
- Risk detection
- Multi-cloud support
- Automation
Pros
- Strong compliance features
- Enterprise-grade
Cons
- Complex configuration
- Requires expertise
Platforms / Deployment
- Cloud
Security & Compliance
- Compliance frameworks supported
Integrations & Ecosystem
- Cloud platforms
- APIs
Support & Community
Enterprise support.
#10 — AWS GuardDuty
Short description: A native AWS threat detection service providing workload-level security insights.
Key Features
- Threat detection
- Continuous monitoring
- Integration with AWS services
- Risk alerts
- Anomaly detection
Pros
- Native AWS integration
- Easy setup
Cons
- AWS-focused
- Limited multi-cloud support
Platforms / Deployment
- Cloud
Security & Compliance
- AWS compliance support
Integrations & Ecosystem
- AWS services
- APIs
Support & Community
Strong AWS ecosystem support.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| SentinelOne | AI protection | Web | Cloud | AI runtime security | N/A |
| Prisma Cloud | Enterprise | Web | Cloud | Full-stack security | N/A |
| Microsoft Defender | Azure users | Web | Cloud | Native integration | N/A |
| Wiz | Modern cloud teams | Web | Cloud | Agentless scanning | N/A |
| Orca Security | Visibility | Web | Cloud | Deep scanning | N/A |
| Aqua Security | Containers | Web | Hybrid | Kubernetes security | N/A |
| Sysdig | Kubernetes | Web | Cloud | Runtime detection | N/A |
| VMware Carbon Black | Enterprise | Web | Hybrid | Endpoint integration | N/A |
| CloudGuard | Compliance | Web | Cloud | Policy management | N/A |
| AWS GuardDuty | AWS users | Web | Cloud | Native detection | N/A |
Evaluation & Scoring of CWPP Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| SentinelOne | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.5 |
| Prisma Cloud | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.5 |
| Microsoft Defender | 8 | 8 | 9 | 9 | 8 | 8 | 8 | 8.3 |
| Wiz | 9 | 9 | 8 | 8 | 9 | 8 | 7 | 8.4 |
| Orca Security | 9 | 8 | 8 | 8 | 9 | 8 | 7 | 8.3 |
| Aqua Security | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.9 |
| Sysdig | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.9 |
| Carbon Black | 8 | 7 | 7 | 8 | 8 | 8 | 7 | 7.8 |
| CloudGuard | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 8.0 |
| AWS GuardDuty | 7 | 9 | 7 | 8 | 8 | 8 | 8 | 7.8 |
How to interpret scores:
- Scores are comparative across tools
- Higher scores indicate stronger overall capability
- Enterprise tools excel in integrations and depth
- Agentless tools score higher in ease of use
- Choose based on cloud architecture and needs
Which CWPP Tool Is Right for You?
Solo / Freelancer
Use AWS GuardDuty for simplicity and quick deployment.
SMB
Use Wiz or Orca Security for ease of use and visibility.
Mid-Market
Use Sysdig or Aqua Security for container-focused environments.
Enterprise
Use Prisma Cloud, SentinelOne, or Microsoft Defender.
Budget vs Premium
- Budget: AWS GuardDuty
- Premium: Prisma Cloud, SentinelOne
Feature Depth vs Ease of Use
- Deep features: Prisma Cloud
- Ease of use: Wiz
Integrations & Scalability
Best: Microsoft Defender, Prisma Cloud
Security & Compliance Needs
Best: CloudGuard, Prisma Cloud
Frequently Asked Questions (FAQs)
1. What is CWPP?
A solution that protects cloud workloads like VMs and containers.
2. How is CWPP different from CSPM?
CWPP protects workloads at runtime, while CSPM focuses on configurations.
3. Do CWPP tools support multi-cloud?
Yes, most modern tools support multi-cloud environments.
4. Are CWPP tools agent-based?
Some are agent-based, others are agentless.
5. Can CWPP detect runtime threats?
Yes, that is a core capability.
6. Do they support containers?
Yes, especially Kubernetes environments.
7. Are CWPP tools expensive?
Pricing varies by features and scale.
8. Who should use CWPP tools?
Organizations using cloud workloads.
9. Can CWPP integrate with DevOps?
Yes, most tools support CI/CD pipelines.
10. What is the biggest benefit?
Real-time protection of cloud workloads.
Conclusion
Cloud Workload Protection Platforms are essential for securing modern cloud environments where workloads are dynamic, distributed, and constantly evolving. By providing real-time visibility, threat detection, and automated response capabilities, CWPP tools help organizations reduce risk and protect critical assets effectively. While enterprise solutions offer comprehensive capabilities and deep integrations, simpler tools can still provide strong protection for smaller environments. The right approach is to evaluate your cloud architecture, shortlist a few CWPP tools, and validate their effectiveness through real-world testing before committing to a long-term solution.