Introduction
Penetration Testing Tools are specialized security solutions used to simulate real-world cyberattacks in order to identify vulnerabilities in systems, networks, and applications. Unlike basic vulnerability scanners, these tools actively exploit weaknesses to assess how deeply an attacker could penetrate an environment and what damage could be done.
As organizations increasingly rely on digital infrastructure, proactive security testing has become essential. Penetration testing tools help uncover hidden risks, validate defenses, and strengthen overall cybersecurity posture. From web applications and APIs to wireless networks and cloud environments, these tools play a critical role in modern security operations.
Common Use Cases
- Simulating real-world cyberattacks to test defenses
- Identifying exploitable vulnerabilities in applications
- Network security assessments and audits
- Testing authentication, authorization, and access controls
- Securing APIs, cloud infrastructure, and endpoints
What Buyers Should Evaluate
- Scope of testing (network, web, wireless, API)
- Automation vs manual testing capabilities
- Ease of use and learning curve
- Integration with security workflows
- Reporting and documentation features
- Support for compliance requirements
- Extensibility and plugin ecosystem
- Performance and scalability
- Cost and licensing model
Best for: Security professionals, ethical hackers, DevSecOps teams, IT auditors, and enterprises with mature security practices.
Not ideal for: Non-technical users or organizations without dedicated security expertise; simpler vulnerability scanners may be more appropriate in those cases.
Key Trends in Penetration Testing Tools
- Automation combined with manual testing workflows
- Integration with DevSecOps pipelines (shift-left security)
- AI-assisted vulnerability discovery and exploitation
- Cloud and container penetration testing capabilities
- API security testing becoming a priority
- Expansion of wireless and IoT testing tools
- Modular and plugin-based architectures
- Improved reporting and collaboration features
- Open-source tools continuing to evolve rapidly
- Focus on real-time attack simulation and validation
How We Selected These Tools (Methodology)
- Strong industry adoption and credibility
- Proven effectiveness in real-world testing
- Comprehensive feature sets across testing domains
- Availability of community and documentation
- Balance between open-source and commercial tools
- Support for modern infrastructure environments
- Integration capabilities with security ecosystems
- Suitability across different skill levels and use cases
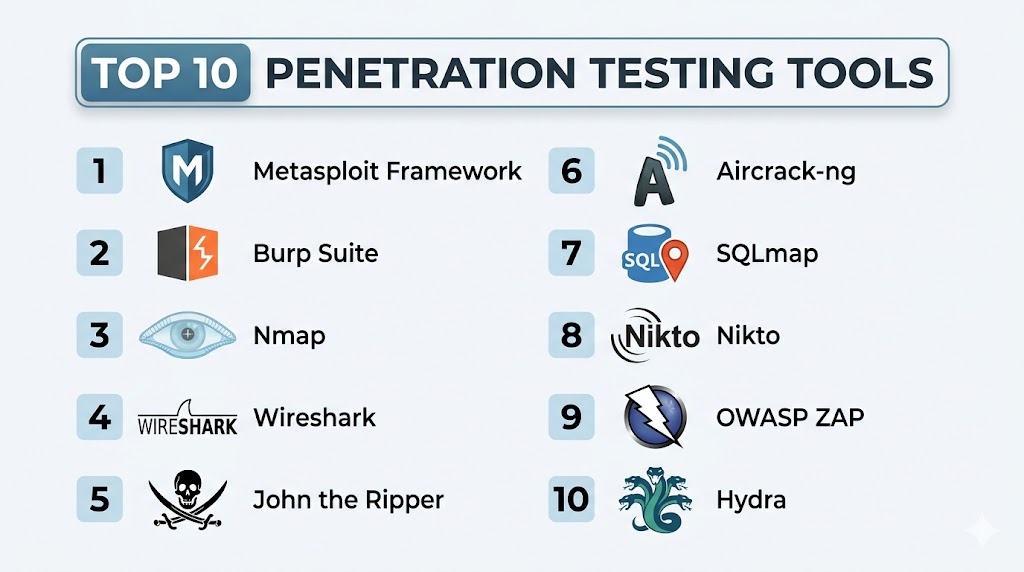
Top 10 Penetration Testing Tools Tools
#1 — Metasploit Framework
Short description: A widely used penetration testing platform for developing and executing exploit code against target systems.
Key Features
- Extensive exploit database
- Payload generation and delivery
- Post-exploitation tools
- Automation and scripting
- Integration with vulnerability scanners
- Modular architecture
Pros
- Highly powerful and flexible
- Industry-standard tool
Cons
- Requires technical expertise
- Can be complex for beginners
Platforms / Deployment
- Windows / Linux / macOS
- Self-hosted
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
Metasploit integrates with various tools to enhance testing workflows.
- Vulnerability scanners
- APIs
- Security frameworks
Support & Community
Strong open-source community and extensive documentation.
#2 — Burp Suite
Short description: A leading web application security testing platform used for both manual and automated testing.
Key Features
- Web vulnerability scanning
- Proxy-based traffic analysis
- Automated scanning
- API testing
- Extension marketplace
Pros
- Highly customizable
- Strong for web security testing
Cons
- Steep learning curve
- Limited network testing
Platforms / Deployment
- Windows / macOS / Linux
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- CI/CD pipelines
- APIs
- Extensions
Support & Community
Large community and strong documentation.
#3 — Nmap
Short description: A network scanning tool used for discovery and security auditing.
Key Features
- Network discovery
- Port scanning
- OS detection
- Scriptable scanning engine
- Service version detection
Pros
- Fast and reliable
- Highly flexible
Cons
- Command-line interface
- Requires expertise
Platforms / Deployment
- Windows / Linux / macOS
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Scripts (NSE)
- APIs
- Automation tools
Support & Community
Strong global community support.
#4 — Wireshark
Short description: A network protocol analyzer used for deep packet inspection and traffic analysis.
Key Features
- Packet capture and analysis
- Protocol decoding
- Real-time traffic monitoring
- Filtering capabilities
- Visualization tools
Pros
- Detailed network insights
- Free and widely used
Cons
- Complex interface
- Not a direct exploitation tool
Platforms / Deployment
- Windows / Linux / macOS
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Plugins
- Network tools
Support & Community
Extensive community and learning resources.
#5 — John the Ripper
Short description: A password-cracking tool used to test password strength and authentication security.
Key Features
- Password cracking
- Dictionary attacks
- Brute-force attacks
- Multi-format support
- GPU acceleration
Pros
- Effective for password testing
- Highly customizable
Cons
- Limited scope
- Requires expertise
Platforms / Deployment
- Windows / Linux / macOS
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- CLI tools
- Scripts
Support & Community
Strong open-source community.
#6 — Aircrack-ng
Short description: A suite of tools for testing wireless network security.
Key Features
- Wi-Fi password cracking
- Packet capture
- Network monitoring
- WPA/WPA2 testing
- Wireless analysis
Pros
- Specialized for wireless security
- Open-source
Cons
- Limited to Wi-Fi testing
- Requires technical setup
Platforms / Deployment
- Linux / Windows
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Wireless adapters
- CLI tools
Support & Community
Active community support.
#7 — SQLmap
Short description: An automated tool for detecting and exploiting SQL injection vulnerabilities.
Key Features
- SQL injection detection
- Database takeover
- Automated exploitation
- Support for multiple DBMS
- Command-line interface
Pros
- Highly effective
- Automation-focused
Cons
- Limited scope
- Requires knowledge of databases
Platforms / Deployment
- Linux / Windows
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Scripts
- APIs
Support & Community
Strong community support.
#8 — Nikto
Short description: A web server scanner that identifies vulnerabilities and outdated components.
Key Features
- Web server scanning
- Detection of outdated software
- Plugin-based scanning
- Command-line interface
Pros
- Lightweight
- Open-source
Cons
- Limited modern features
- Not enterprise-grade
Platforms / Deployment
- Linux / Windows
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- CLI tools
- Scripts
Support & Community
Active open-source community.
#9 — OWASP ZAP
Short description: An open-source web application security scanner maintained by the OWASP community.
Key Features
- Automated scanning
- Proxy-based testing
- API security testing
- Passive and active scanning
- Plugin support
Pros
- Beginner-friendly
- Free and open-source
Cons
- Limited advanced features
- Slower compared to premium tools
Platforms / Deployment
- Windows / Linux / macOS
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- CI/CD tools
- APIs
- Plugins
Support & Community
Strong OWASP community support.
#10 — Hydra
Short description: A fast password-cracking tool used for testing login security across multiple protocols.
Key Features
- Brute-force attacks
- Multi-protocol support
- Fast performance
- CLI-based operation
Pros
- Fast and efficient
- Supports many protocols
Cons
- Limited to password attacks
- Requires expertise
Platforms / Deployment
- Linux / Windows
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Scripts
- CLI automation
Support & Community
Active open-source community.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Metasploit | Exploitation | Cross-platform | Self-hosted | Exploit framework | N/A |
| Burp Suite | Web testing | Cross-platform | Self-hosted | Proxy analysis | N/A |
| Nmap | Network scanning | Cross-platform | Self-hosted | Port scanning | N/A |
| Wireshark | Traffic analysis | Cross-platform | Self-hosted | Packet inspection | N/A |
| John the Ripper | Password testing | Cross-platform | Self-hosted | Password cracking | N/A |
| Aircrack-ng | Wireless testing | Linux, Windows | Self-hosted | Wi-Fi cracking | N/A |
| SQLmap | SQL injection | Linux, Windows | Self-hosted | Automated exploitation | N/A |
| Nikto | Web scanning | Linux, Windows | Self-hosted | Lightweight scanning | N/A |
| OWASP ZAP | Web security | Cross-platform | Self-hosted | Beginner-friendly | N/A |
| Hydra | Password attacks | Linux, Windows | Self-hosted | Fast brute force | N/A |
Evaluation & Scoring of Penetration Testing Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Metasploit | 9 | 6 | 9 | 8 | 9 | 8 | 8 | 8.4 |
| Burp Suite | 9 | 6 | 8 | 8 | 8 | 8 | 7 | 8.0 |
| Nmap | 8 | 6 | 7 | 7 | 9 | 8 | 9 | 7.9 |
| Wireshark | 7 | 6 | 7 | 7 | 8 | 8 | 9 | 7.6 |
| John the Ripper | 7 | 6 | 6 | 6 | 8 | 7 | 9 | 7.3 |
| Aircrack-ng | 7 | 6 | 6 | 6 | 7 | 7 | 9 | 7.2 |
| SQLmap | 8 | 6 | 6 | 6 | 8 | 7 | 9 | 7.5 |
| Nikto | 6 | 6 | 5 | 5 | 6 | 6 | 9 | 6.3 |
| OWASP ZAP | 7 | 8 | 7 | 7 | 7 | 8 | 9 | 7.8 |
| Hydra | 7 | 6 | 6 | 6 | 8 | 7 | 9 | 7.3 |
How to interpret scores:
- Scores are relative comparisons across tools
- Higher scores indicate stronger overall capability
- Open-source tools offer strong value but require expertise
- Choose based on use case rather than score alone
Which Penetration Testing Tools Tool Is Right for You?
Solo / Freelancer
Use OWASP ZAP or Nmap for simple and effective testing.
SMB
Use Burp Suite or Metasploit for broader testing capabilities.
Mid-Market
Use Metasploit + Burp Suite combination for complete coverage.
Enterprise
Use multiple tools together (Metasploit, Burp Suite, Nmap) for full security testing.
Budget vs Premium
- Budget: OWASP ZAP, Nikto, Nmap
- Premium: Burp Suite
Feature Depth vs Ease of Use
- Deep features: Metasploit
- Ease of use: OWASP ZAP
Integrations & Scalability
Best combination: Metasploit + Burp Suite
Security & Compliance Needs
Use tools with reporting and documentation features like Burp Suite.
Frequently Asked Questions (FAQs)
1. What are penetration testing tools?
They simulate attacks to identify exploitable vulnerabilities.
2. Are these tools legal to use?
Yes, but only on systems you own or have permission to test.
3. Do I need coding skills?
Helpful but not always required.
4. What is the difference from vulnerability scanners?
Pen testing tools actively exploit vulnerabilities.
5. Can beginners use these tools?
Some tools are beginner-friendly; others require expertise.
6. Are open-source tools enough?
Yes, but enterprise tools provide more features.
7. How often should testing be done?
Regularly, especially after changes.
8. Can these tools integrate with DevOps?
Yes, many support CI/CD pipelines.
9. What is the biggest risk?
Misuse without proper authorization.
10. Which tool is best?
Depends on your use case and expertise.
Conclusion
Penetration Testing Tools are essential for proactively identifying and validating security weaknesses before attackers can exploit them. From network scanning to advanced exploitation frameworks, these tools provide deep insights into system vulnerabilities and real-world attack scenarios. While open-source tools offer flexibility and cost advantages, commercial tools often provide enhanced usability and support. The right approach is rarely a single tool—most organizations benefit from combining multiple tools to cover different testing areas. Start by selecting a few tools that align with your needs, test them in controlled environments, and build a penetration testing strategy that fits your security maturity and operational goals.