Introduction
Exposure Management Platforms are modern cybersecurity solutions designed to provide a unified view of an organization’s security risks across its entire attack surface. Unlike traditional tools that operate in silos (like vulnerability scanners, ASM, or EDR), exposure management platforms aggregate data from multiple sources to prioritize real-world risk and guide remediation efforts.
These platforms focus on risk-based prioritization, helping security teams understand which vulnerabilities actually matter based on exploitability, business context, and attacker behavior. As organizations deal with fragmented security stacks and increasing attack complexity, exposure management is becoming a critical layer for decision-making and risk reduction.
Common Use Cases
- Consolidating security findings from multiple tools
- Prioritizing vulnerabilities based on real-world risk
- Managing exposures across cloud, endpoints, and applications
- Supporting compliance and audit processes
- Automating remediation workflows
What Buyers Should Evaluate
- Risk prioritization accuracy
- Integration with existing security tools
- Data aggregation and normalization capabilities
- Ease of use and dashboards
- Automation and remediation workflows
- Scalability across environments
- Threat intelligence integration
- Reporting and compliance features
- Cost vs value
Best for: Security teams, CISOs, enterprises, and organizations with multiple security tools needing centralized risk visibility.
Not ideal for: Small teams with minimal infrastructure or those needing only basic vulnerability scanning.
Key Trends in Exposure Management Platforms
- Risk-based prioritization replacing severity-based scoring
- Consolidation of multiple security tools into unified platforms
- AI-driven exposure analysis and attack path modeling
- Integration with DevSecOps workflows
- Continuous monitoring across hybrid environments
- Expansion into attack surface and threat intelligence domains
- Automation of remediation workflows
- Focus on business impact-driven security decisions
- API-first architectures for integration flexibility
- Real-time dashboards and executive reporting
How We Selected These Tools (Methodology)
- Strong market adoption and recognition
- Proven risk prioritization capabilities
- Integration with multiple security tools and ecosystems
- Support for modern infrastructure (cloud, hybrid)
- Availability of automation and remediation workflows
- Usability across different organization sizes
- Balanced mix of enterprise and SMB-friendly tools
- Strong documentation and support availability
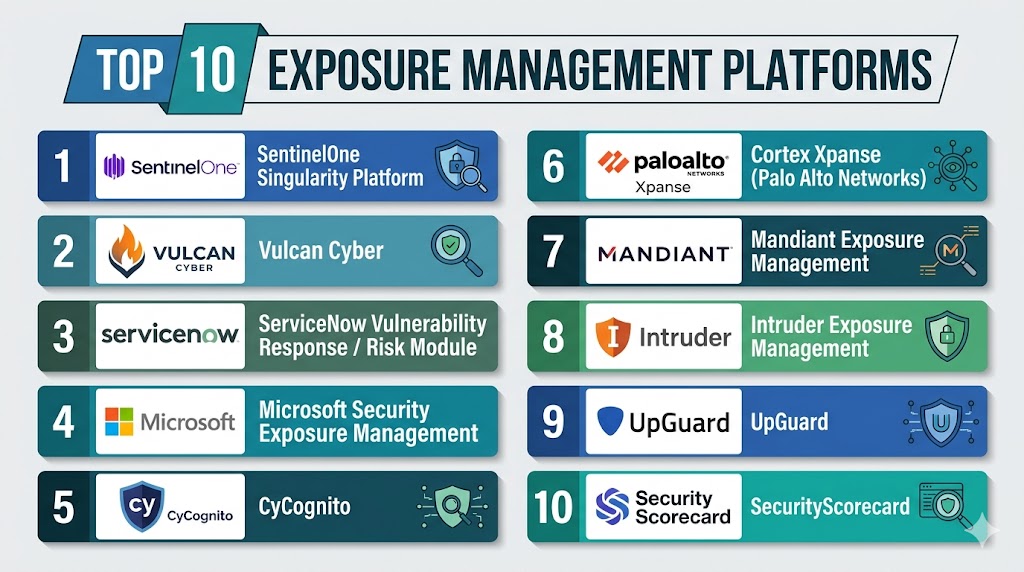
Top 10 Exposure Management Platforms
#1 — SentinelOne Singularity Platform
Short description: A unified security platform that combines endpoint, cloud, and identity risk insights with exposure management capabilities.
Key Features
- Unified risk visibility
- AI-driven threat detection
- Exposure prioritization
- Endpoint and cloud integration
- Real-time analytics
- Automation workflows
Pros
- Strong AI capabilities
- Unified platform approach
Cons
- Complex setup
- Premium pricing
Platforms / Deployment
- Cloud
Security & Compliance
- RBAC, encryption
- Compliance support varies
Integrations & Ecosystem
- EDR tools
- SIEM platforms
- APIs
- Cloud services
Support & Community
Enterprise support with strong documentation.
#2 — Vulcan Cyber
Short description: A dedicated exposure management platform focused on risk prioritization and remediation orchestration.
Key Features
- Risk-based prioritization
- Data aggregation from multiple tools
- Remediation orchestration
- Workflow automation
- Vulnerability correlation
Pros
- Strong prioritization engine
- Excellent remediation workflows
Cons
- Depends on integrations
- Limited standalone scanning
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Vulnerability scanners
- SIEM tools
- Ticketing systems
- APIs
Support & Community
Strong enterprise support.
#3 — ServiceNow Vulnerability Response / Risk Module
Short description: A platform that integrates exposure management into IT service workflows for remediation and tracking.
Key Features
- Vulnerability response workflows
- Risk prioritization
- Integration with ITSM
- Automation
- Reporting dashboards
Pros
- Strong workflow integration
- Scalable for enterprises
Cons
- Requires ServiceNow ecosystem
- Complex setup
Platforms / Deployment
- Cloud
Security & Compliance
- SSO, RBAC, audit logs
- Compliance support varies
Integrations & Ecosystem
- ITSM tools
- Security tools
- APIs
Support & Community
Extensive enterprise support and documentation.
#4 — Microsoft Security Exposure Management
Short description: A risk-focused platform integrated into Microsoft security ecosystem for unified exposure visibility.
Key Features
- Risk prioritization
- Integration with Microsoft tools
- Continuous monitoring
- Threat intelligence integration
- Asset visibility
Pros
- Seamless Microsoft integration
- Easy deployment
Cons
- Limited outside ecosystem
- Best for Microsoft environments
Platforms / Deployment
- Cloud
Security & Compliance
- SSO, MFA, RBAC
- Compliance support varies
Integrations & Ecosystem
- Microsoft Defender
- Azure services
- APIs
Support & Community
Strong enterprise support.
#5 — CyCognito
Short description: A platform that combines attack surface management with exposure prioritization.
Key Features
- External asset discovery
- Risk prioritization
- Continuous monitoring
- Exposure validation
- Cloud visibility
Pros
- Deep discovery capabilities
- Strong analytics
Cons
- Premium pricing
- Complex interface
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM tools
- APIs
- Cloud platforms
Support & Community
Enterprise support.
#6 — Cortex Xpanse
Short description: A platform providing real-time visibility into external exposures and attack surfaces.
Key Features
- Real-time asset discovery
- Exposure detection
- Risk scoring
- Continuous monitoring
- Misconfiguration alerts
Pros
- Real-time insights
- Strong enterprise capabilities
Cons
- Requires integration
- Enterprise-focused
Platforms / Deployment
- Cloud
Security & Compliance
- RBAC, encryption
- Compliance varies
Integrations & Ecosystem
- SIEM
- SOAR
- APIs
Support & Community
Enterprise support.
#7 — Mandiant Exposure Management
Short description: A platform leveraging threat intelligence to identify and prioritize exposures.
Key Features
- Threat intelligence integration
- Exposure prioritization
- Continuous monitoring
- Risk analysis
- Asset discovery
Pros
- Strong intelligence insights
- Trusted brand
Cons
- Premium pricing
- Enterprise focus
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Security platforms
- APIs
Support & Community
Enterprise support.
#8 — Intruder Exposure Management
Short description: A simplified platform focused on continuous vulnerability monitoring and exposure management.
Key Features
- Continuous scanning
- Risk prioritization
- Alerts
- Cloud integration
- Dashboard visibility
Pros
- Easy to use
- Suitable for SMBs
Cons
- Limited advanced features
- Less scalable
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Cloud platforms
- APIs
Support & Community
Responsive support.
#9 — UpGuard
Short description: A platform focused on external risk and vendor exposure management.
Key Features
- Risk scoring
- Vendor risk management
- Continuous monitoring
- Reporting
- Exposure tracking
Pros
- Strong vendor risk capabilities
- User-friendly
Cons
- Limited deep scanning
- Less technical depth
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- Security tools
Support & Community
Good onboarding and support.
#10 — SecurityScorecard
Short description: A security ratings platform offering visibility into exposure risk across organizations and vendors.
Key Features
- Security scoring
- Risk insights
- External monitoring
- Vendor risk analysis
- Reporting
Pros
- Easy-to-understand metrics
- Strong reporting
Cons
- Limited technical depth
- Focus on visibility
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- Security tools
Support & Community
Strong enterprise support.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| SentinelOne | Unified security | Web | Cloud | AI-driven analytics | N/A |
| Vulcan Cyber | Risk prioritization | Web | Cloud | Remediation workflows | N/A |
| ServiceNow | ITSM integration | Web | Cloud | Workflow automation | N/A |
| Microsoft Security | Microsoft ecosystem | Web | Cloud | Native integration | N/A |
| CyCognito | External exposure | Web | Cloud | Deep discovery | N/A |
| Cortex Xpanse | Enterprise ASM | Web | Cloud | Real-time visibility | N/A |
| Mandiant | Threat intelligence | Web | Cloud | Risk insights | N/A |
| Intruder | SMBs | Web | Cloud | Ease of use | N/A |
| UpGuard | Vendor risk | Web | Cloud | Third-party monitoring | N/A |
| SecurityScorecard | Risk scoring | Web | Cloud | Security ratings | N/A |
Evaluation & Scoring of Exposure Management Platforms
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| SentinelOne | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.5 |
| Vulcan Cyber | 9 | 7 | 9 | 8 | 8 | 8 | 8 | 8.4 |
| ServiceNow | 8 | 7 | 9 | 9 | 8 | 9 | 7 | 8.3 |
| Microsoft | 8 | 8 | 9 | 9 | 8 | 8 | 8 | 8.3 |
| CyCognito | 9 | 7 | 8 | 8 | 9 | 8 | 7 | 8.2 |
| Cortex Xpanse | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.4 |
| Mandiant | 9 | 7 | 8 | 8 | 9 | 8 | 7 | 8.2 |
| Intruder | 7 | 9 | 7 | 7 | 8 | 7 | 8 | 7.9 |
| UpGuard | 7 | 8 | 7 | 7 | 8 | 7 | 8 | 7.8 |
| SecurityScorecard | 7 | 9 | 7 | 7 | 8 | 8 | 8 | 8.0 |
How to interpret scores:
- Scores are relative comparisons
- Higher scores indicate stronger overall capabilities
- Enterprise platforms score higher in integrations and features
- Simpler tools score higher in usability and value
- Choose based on organizational needs
Which Exposure Management Platform Is Right for You?
Solo / Freelancer
Use Intruder or UpGuard for simplicity and ease of use.
SMB
Use Intruder or SecurityScorecard for affordability and visibility.
Mid-Market
Use Vulcan Cyber or Microsoft Security Exposure Management.
Enterprise
Use SentinelOne, Cortex Xpanse, or ServiceNow.
Budget vs Premium
- Budget: Intruder, UpGuard
- Premium: SentinelOne, Cortex, Mandiant
Feature Depth vs Ease of Use
- Deep features: Vulcan Cyber, Cortex Xpanse
- Ease of use: Intruder, UpGuard
Integrations & Scalability
Best: ServiceNow, Microsoft, Cortex
Security & Compliance Needs
Best: Microsoft, ServiceNow
Frequently Asked Questions (FAQs)
1. What is exposure management?
It is the process of identifying and prioritizing security risks across an organization.
2. How is it different from vulnerability management?
Exposure management focuses on real-world risk and prioritization.
3. Do these tools replace vulnerability scanners?
No, they integrate and enhance them.
4. Are these platforms cloud-based?
Most are cloud-based solutions.
5. Who should use exposure management tools?
Organizations with multiple security tools.
6. Can these tools automate remediation?
Yes, many include automation workflows.
7. Are they suitable for small businesses?
Some tools are designed for SMBs.
8. Do they integrate with DevOps?
Yes, modern platforms support DevOps integration.
9. What is the biggest benefit?
Centralized risk visibility.
10. How do I choose the right platform?
Evaluate based on integrations, scale, and features.
Conclusion
Exposure Management Platforms are redefining how organizations approach cybersecurity by shifting focus from isolated vulnerabilities to real-world risk prioritization. By aggregating data from multiple security tools and providing contextual insights, these platforms enable teams to make smarter, faster decisions. While enterprise solutions offer deep integrations and advanced capabilities, smaller organizations can still benefit from simplified platforms that deliver strong visibility and control. The best choice depends on your existing security stack, operational complexity, and risk management goals. Start by identifying your key exposures, shortlist a few platforms, and validate their effectiveness through real-world testing before full adoption.