Introduction
Attack Surface Management (ASM) tools help organizations discover, monitor, and secure all externally exposed assets across the internet. This includes domains, subdomains, IPs, cloud services, APIs, shadow IT, and forgotten assets that attackers often exploit first. Unlike traditional vulnerability scanners that focus on known systems, ASM tools continuously map the entire external attack surface—including unknown and unmanaged assets.
As digital footprints expand through cloud adoption, SaaS usage, and remote work, the attack surface becomes dynamic and difficult to control. ASM tools provide continuous visibility, risk prioritization, and actionable insights to reduce exposure before attackers can exploit it.
Common Use Cases
- Discovering unknown internet-facing assets
- Monitoring shadow IT and misconfigured cloud services
- Continuous external risk monitoring
- Identifying exposed credentials and sensitive data
- Supporting compliance and security audits
What Buyers Should Evaluate
- Asset discovery depth and accuracy
- Continuous monitoring capabilities
- Risk prioritization and scoring
- Ease of use and dashboards
- Integration with security tools (SIEM, SOAR)
- Automation and alerting capabilities
- Coverage across cloud, SaaS, and APIs
- Scalability across global infrastructure
- Cost vs value
Best for: Security teams, CISOs, IT operations, and enterprises with large or dynamic external infrastructure.
Not ideal for: Organizations with very limited digital presence or those only needing internal vulnerability scanning.
Key Trends in Attack Surface Management (ASM)
- Continuous external asset discovery replacing periodic scans
- AI-driven risk prioritization and attack path analysis
- Integration with threat intelligence platforms
- Expansion into digital risk protection (DRP)
- Cloud and SaaS visibility becoming critical
- Automation of remediation workflows
- Consolidation into unified security platforms
- API and microservices exposure monitoring
- Focus on shadow IT and unmanaged assets
- Real-time alerting and incident response integration
How We Selected These Tools (Methodology)
- Strong market presence and adoption
- Proven external asset discovery capabilities
- Advanced risk scoring and prioritization
- Integration with broader security ecosystems
- Support for cloud and modern infrastructure
- Usability across different organization sizes
- Availability of documentation and support
- Balance between enterprise and SMB solutions
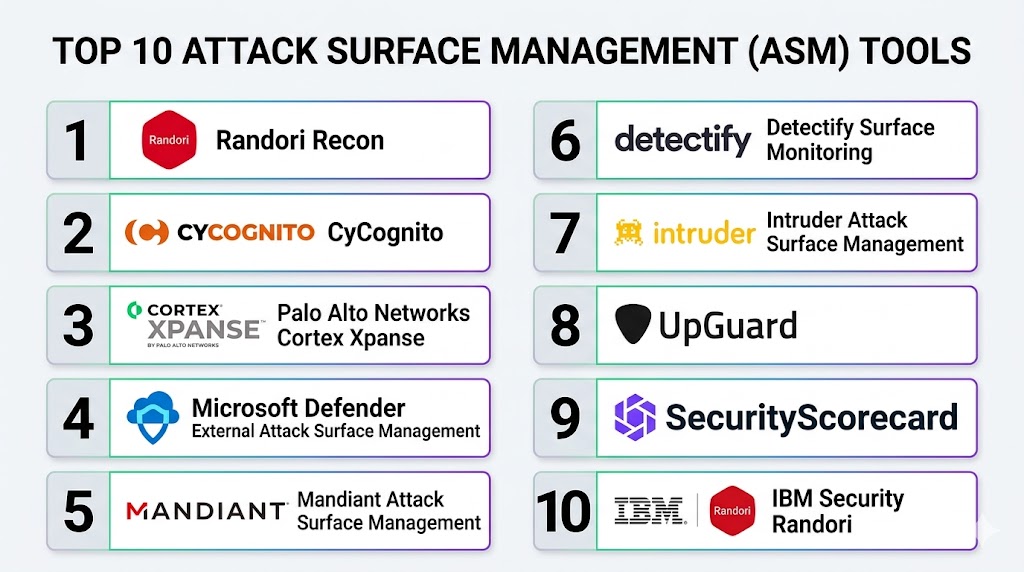
Top 10 Attack Surface Management (ASM) Tools
#1 — Randori Recon
Short description: A platform focused on attacker-perspective reconnaissance to identify high-risk external exposures.
Key Features
- Continuous external asset discovery
- Attack-path prioritization
- Risk-based scoring
- Real-time monitoring
- Automated reconnaissance
- Exposure validation
Pros
- Attacker-centric insights
- Strong prioritization
Cons
- Enterprise-focused pricing
- Requires security expertise
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM tools
- APIs
- Security platforms
Support & Community
Enterprise support with documentation and onboarding resources.
#2 — CyCognito
Short description: A comprehensive ASM platform that maps and monitors external attack surfaces with deep discovery capabilities.
Key Features
- Automated asset discovery
- Continuous monitoring
- Risk prioritization
- Exposure validation
- Cloud visibility
- Shadow IT detection
Pros
- Deep discovery capabilities
- Strong analytics
Cons
- Premium pricing
- Complexity for beginners
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM tools
- APIs
- Cloud platforms
Support & Community
Strong enterprise support and onboarding.
#3 — Cortex Xpanse
Short description: An ASM solution offering real-time visibility into global attack surfaces and misconfigurations.
Key Features
- Real-time asset discovery
- Global internet scanning
- Risk detection
- Misconfiguration alerts
- Continuous monitoring
- Integration with security platforms
Pros
- Real-time insights
- Strong enterprise capabilities
Cons
- Requires integration setup
- Enterprise-focused
Platforms / Deployment
- Cloud
Security & Compliance
- RBAC, encryption
- Compliance support varies
Integrations & Ecosystem
- SIEM
- SOAR
- APIs
Support & Community
Enterprise-grade support.
#4 — Microsoft Defender External Attack Surface Management
Short description: A cloud-based ASM solution integrated into the Microsoft security ecosystem.
Key Features
- External asset discovery
- Continuous monitoring
- Risk prioritization
- Integration with Microsoft security tools
- Threat intelligence integration
Pros
- Seamless Microsoft integration
- Easy deployment
Cons
- Best suited for Microsoft environments
- Limited outside ecosystem
Platforms / Deployment
- Cloud
Security & Compliance
- SSO, MFA, RBAC
- Compliance support varies
Integrations & Ecosystem
- Microsoft security tools
- APIs
- SIEM
Support & Community
Strong enterprise support.
#5 — Mandiant Attack Surface Management
Short description: A threat-focused ASM solution leveraging advanced intelligence and incident response expertise.
Key Features
- Asset discovery
- Threat intelligence integration
- Risk prioritization
- Continuous monitoring
- Exposure analysis
Pros
- Strong threat intelligence
- Trusted brand
Cons
- Premium pricing
- Enterprise-focused
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Security platforms
- APIs
- SIEM
Support & Community
Enterprise-level support.
#6 — Detectify Surface Monitoring
Short description: A crowdsourced security testing platform focused on continuous monitoring of external assets.
Key Features
- Continuous monitoring
- Asset discovery
- Crowdsourced vulnerability insights
- Risk scoring
- Alerts and reporting
Pros
- Innovative testing approach
- Easy to use
Cons
- Limited enterprise depth
- Smaller ecosystem
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- DevOps tools
Support & Community
Good documentation and support.
#7 — Intruder ASM
Short description: A user-friendly ASM tool designed for continuous exposure monitoring.
Key Features
- Continuous scanning
- Asset discovery
- Risk prioritization
- Alerts
- Cloud integration
Pros
- Easy to use
- Good for SMBs
Cons
- Limited advanced features
- Not ideal for large enterprises
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Cloud platforms
- APIs
Support & Community
Responsive support.
#8 — UpGuard
Short description: A digital risk and ASM platform focusing on external security posture and third-party risk.
Key Features
- Attack surface monitoring
- Vendor risk management
- Risk scoring
- Continuous monitoring
- Reporting
Pros
- Strong vendor risk capabilities
- Easy dashboards
Cons
- Less focus on deep scanning
- Limited customization
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- Security tools
Support & Community
Good support and onboarding.
#9 — SecurityScorecard
Short description: A security ratings platform that provides visibility into external attack surfaces and risk posture.
Key Features
- Security scoring
- External asset monitoring
- Risk insights
- Vendor risk management
- Reporting
Pros
- Easy to understand scoring
- Strong reporting
Cons
- Limited technical depth
- Focus on visibility over action
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- Security tools
Support & Community
Strong enterprise support.
#10 — IBM Security Randori
Short description: An ASM and offensive security platform focusing on attacker behavior and exposure management.
Key Features
- Continuous discovery
- Attack simulation
- Risk prioritization
- Exposure validation
- Threat insights
Pros
- Strong attacker perspective
- Advanced capabilities
Cons
- Enterprise-focused
- Requires expertise
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- Security tools
Support & Community
Enterprise support and documentation.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Randori Recon | Offensive ASM | Web | Cloud | Attacker perspective | N/A |
| CyCognito | Deep discovery | Web | Cloud | Shadow IT detection | N/A |
| Cortex Xpanse | Enterprise ASM | Web | Cloud | Real-time scanning | N/A |
| Microsoft Defender ASM | Microsoft users | Web | Cloud | Native integration | N/A |
| Mandiant ASM | Threat intelligence | Web | Cloud | Threat insights | N/A |
| Detectify | Continuous monitoring | Web | Cloud | Crowdsourced testing | N/A |
| Intruder ASM | SMBs | Web | Cloud | Ease of use | N/A |
| UpGuard | Vendor risk | Web | Cloud | Third-party monitoring | N/A |
| SecurityScorecard | Risk scoring | Web | Cloud | Security ratings | N/A |
| IBM Randori | Advanced ASM | Web | Cloud | Attack simulation | N/A |
Evaluation & Scoring of Attack Surface Management (ASM) Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Randori Recon | 9 | 7 | 8 | 8 | 9 | 8 | 7 | 8.2 |
| CyCognito | 9 | 7 | 8 | 8 | 9 | 8 | 7 | 8.2 |
| Cortex Xpanse | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.4 |
| Microsoft ASM | 8 | 8 | 9 | 9 | 8 | 8 | 8 | 8.3 |
| Mandiant ASM | 9 | 7 | 8 | 8 | 9 | 8 | 7 | 8.2 |
| Detectify | 8 | 8 | 7 | 7 | 8 | 7 | 8 | 7.8 |
| Intruder ASM | 7 | 9 | 7 | 7 | 8 | 7 | 8 | 7.9 |
| UpGuard | 7 | 8 | 7 | 7 | 8 | 7 | 8 | 7.7 |
| SecurityScorecard | 7 | 9 | 7 | 7 | 8 | 8 | 8 | 7.9 |
| IBM Randori | 9 | 7 | 8 | 8 | 9 | 8 | 7 | 8.2 |
How to interpret scores:
- Scores are relative comparisons
- Higher scores indicate stronger overall capabilities
- Enterprise tools excel in integrations and scalability
- Simpler tools score higher in usability and value
- Choose based on your specific requirements
Which Attack Surface Management Tool Is Right for You?
Solo / Freelancer
Use Intruder ASM or Detectify for simplicity and quick setup.
SMB
Use UpGuard or Intruder ASM for ease of use and affordability.
Mid-Market
Use CyCognito or Microsoft ASM for balanced features and scalability.
Enterprise
Use Cortex Xpanse, Mandiant ASM, or Randori Recon for advanced capabilities.
Budget vs Premium
- Budget: Intruder ASM, Detectify
- Premium: CyCognito, Cortex Xpanse, Mandiant
Feature Depth vs Ease of Use
- Deep features: CyCognito, Randori
- Ease of use: Intruder, UpGuard
Integrations & Scalability
Best: Cortex Xpanse, Microsoft ASM
Security & Compliance Needs
Best: Microsoft ASM, Cortex Xpanse
Frequently Asked Questions (FAQs)
1. What is Attack Surface Management?
It is the process of identifying and managing all exposed assets on the internet.
2. How is ASM different from vulnerability scanning?
ASM focuses on discovering assets, while scanning identifies vulnerabilities.
3. Do ASM tools run continuously?
Yes, most tools provide continuous monitoring.
4. Are ASM tools cloud-based?
Most modern tools are cloud-based.
5. Who needs ASM tools?
Organizations with internet-facing assets.
6. Can ASM tools detect shadow IT?
Yes, that is a core capability.
7. Do they integrate with SIEM?
Yes, most tools support integrations.
8. Are ASM tools expensive?
Pricing varies based on features and scale.
9. Can small businesses use ASM tools?
Yes, especially lightweight tools.
10. What is the biggest benefit?
Visibility into unknown risks.
Conclusion
Attack Surface Management tools provide critical visibility into the ever-expanding digital footprint of modern organizations. By continuously discovering and monitoring external assets, these tools help security teams stay ahead of potential threats and reduce exposure risks effectively. While enterprise-grade platforms offer deep insights and integrations, smaller organizations can benefit from simpler, user-friendly solutions that still deliver strong value. The best approach is to evaluate your organization’s size, infrastructure complexity, and security maturity before selecting a tool. Start by shortlisting a few platforms, test their capabilities in your environment, and ensure they align with your overall security strategy.