Introduction
Endpoint Detection & Response (EDR) solutions are specialized cybersecurity tools that monitor, detect, and respond to threats targeting endpoints such as desktops, laptops, servers, and mobile devices. Unlike traditional antivirus software, EDR platforms provide continuous monitoring, threat intelligence, and automated remediation to mitigate attacks before they escalate. As endpoints grow in number and complexity, EDR has become critical for modern security strategies.
Real-world use cases include detecting ransomware attacks, monitoring remote worker devices for unusual behavior, responding to phishing incidents, investigating potential insider threats, and securing hybrid work environments. When evaluating EDR tools, buyers should consider detection capabilities, automated response, threat intelligence integration, platform coverage, deployment flexibility, ease of use, integration with existing security stack, scalability, performance, and support.
Best for: IT managers, security teams, and enterprises seeking proactive endpoint protection across hybrid environments. Industries with strict regulatory requirements, such as finance, healthcare, and critical infrastructure, benefit most.
Not ideal for: Very small organizations with minimal endpoints or teams that rely primarily on cloud-native security providers may find simpler antivirus or XDR solutions sufficient.
Key Trends in Endpoint Detection & Response (EDR)
- AI-driven threat detection for zero-day and polymorphic attacks.
- Automated incident response and remediation using playbooks.
- Integration with SIEM and SOAR platforms.
- Cloud-native and hybrid deployment models for flexibility.
- Threat intelligence feeds embedded for contextual alerts.
- Behavior-based monitoring replacing solely signature-based detection.
- Lightweight agents optimized for remote and mobile workforces.
- Emphasis on compliance, such as GDPR and SOC 2.
- Subscription-based pricing and value-focused packages.
- Interoperability with network, IAM, and vulnerability management tools.
How We Selected These Tools (Methodology)
- Evaluated market adoption and enterprise mindshare.
- Assessed feature completeness including detection, response, and automation.
- Reviewed performance and reliability signals for scalability and alert accuracy.
- Considered security posture, certifications, and encryption standards.
- Analyzed integration ecosystems for SIEM, SOAR, and cloud tools.
- Checked suitability across SMB, mid-market, and enterprise segments.
- Evaluated adoption of AI, behavioral analytics, and cloud-native design.
- Considered support and community engagement.
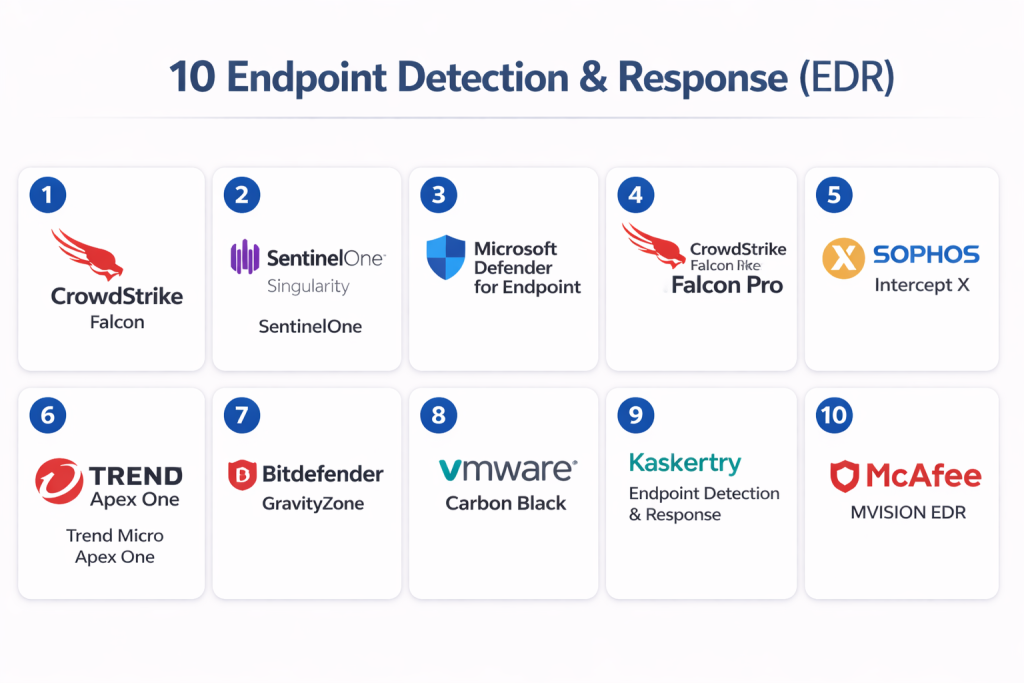
Top 10 Endpoint Detection & Response (EDR) Tools
#1 — CrowdStrike Falcon
Short description: Cloud-native EDR providing real-time threat detection and automated response, suitable for enterprises and hybrid work environments.
Key Features
- AI-driven malware and ransomware detection
- Threat hunting and forensic capabilities
- Automated response playbooks
- Lightweight endpoint agents
- SIEM and SOAR integrations
- Behavioral analytics and anomaly detection
- Cloud-based deployment with global telemetry
Pros
- Rapid detection and containment
- Minimal performance impact on endpoints
- Scalable for large enterprise environments
Cons
- Premium pricing for SMBs
- Limited on-premises deployment options
- Advanced features require higher-tier subscriptions
Platforms / Deployment
- Windows / macOS / Linux / iOS / Android
- Cloud
Security & Compliance
- SOC 2, ISO 27001
- SSO/SAML, MFA, encryption, audit logs
Integrations & Ecosystem
CrowdStrike offers robust integrations with major SIEM and SOAR platforms.
- ServiceNow Security Operations
- Splunk
- Palo Alto Networks Cortex XSOAR
- Microsoft Defender ATP
- APIs for custom integration
Support & Community
- 24/7 support tiers, documentation, and active user forums.
- Comprehensive onboarding guides and training modules.
#2 — SentinelOne Singularity
Short description: Autonomous EDR platform leveraging AI for detection and response, suitable for enterprises and mid-market organizations.
Key Features
- AI-powered prevention and detection
- Automated ransomware rollback
- Cloud and on-premises deployment options
- Behavioral and exploit detection
- Threat intelligence integration
- API access for custom workflows
- Lightweight agents for remote endpoints
Pros
- Automated remediation reduces manual work
- Strong AI detection capabilities
- Flexible deployment options
Cons
- Learning curve for security teams
- Premium pricing for full-feature set
- Some integrations require advanced configuration
Platforms / Deployment
- Windows / macOS / Linux / iOS / Android
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001
- MFA, RBAC, encryption
Integrations & Ecosystem
- SIEM platforms (Splunk, Elastic)
- SOAR tools
- API-based integration
- Vulnerability management connectors
Support & Community
- Varies / Not publicly stated; documentation and training available
#3 — Microsoft Defender for Endpoint
Short description: Enterprise EDR integrated with Microsoft ecosystem, providing threat and vulnerability management across devices.
Key Features
- Deep Windows OS integration
- Cloud-powered behavioral analytics
- Automated endpoint response
- Threat and vulnerability management dashboard
- Integration with Microsoft 365 suite
- Real-time alerts and remediation recommendations
- API access for extended workflows
Pros
- Seamless integration with Microsoft products
- Comprehensive endpoint coverage
- Cost-effective for existing Microsoft customers
Cons
- Limited features outside Microsoft ecosystem
- Mac and Linux coverage less mature
- Learning curve for advanced automation
Platforms / Deployment
- Windows / macOS / Linux / iOS / Android
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR
- SSO/SAML, MFA, encryption
Integrations & Ecosystem
- Microsoft 365 suite
- Azure Sentinel SIEM
- Third-party SIEM via API
- Vulnerability management integrations
Support & Community
- Microsoft support channels and large community forums
#4 — CrowdStrike Falcon Pro
Short description: SMB-focused Falcon version with simplified EDR and automated threat response.
Key Features
- Cloud-native lightweight agent
- Malware and ransomware detection
- Behavioral analytics
- Automated remediation
- Integration with basic SIEM
- Reporting dashboard for SMB IT teams
Pros
- Affordable SMB solution
- Easy deployment and management
- Cloud-first design reduces maintenance overhead
Cons
- Limited advanced threat hunting
- Fewer integrations
- Not ideal for complex enterprise setups
Platforms / Deployment
- Windows / macOS / Linux
- Cloud
Security & Compliance
- SOC 2
- SSO/MFA, encryption
Integrations & Ecosystem
- Basic SIEM integrations
- Limited APIs
Support & Community
- Documentation and standard support
#5 — Sophos Intercept X
Short description: EDR with deep learning AI and exploit prevention for SMBs and enterprises.
Key Features
- AI malware and exploit detection
- Ransomware rollback
- Managed threat response options
- Root cause analysis
- Cloud-based console
- Lightweight agent footprint
- Integration with Sophos XDR
Pros
- Strong ransomware protection
- Easy management across endpoints
- Cloud console simplifies operations
Cons
- Advanced features require premium license
- Less suitable outside Sophos ecosystem
- Some reporting limitations
Platforms / Deployment
- Windows / macOS / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2
- MFA, encryption
Integrations & Ecosystem
- Sophos XDR
- SIEM connectors
- APIs for automation
Support & Community
- Active support channels and documentation
#6 — Trend Micro Apex One
Short description: EDR with AI threat detection, behavioral analysis, and vulnerability protection for enterprises.
Key Features
- Automated threat detection and response
- Behavioral analysis and machine learning
- Vulnerability protection and patch management
- Centralized console
- Threat intelligence feeds
- Cloud and on-premises deployment
- API access
Pros
- Comprehensive detection
- Strong Trend Micro integration
- Scalable for large environments
Cons
- Complex setup for small teams
- Premium features require higher-tier plans
- Agent updates may require management
Platforms / Deployment
- Windows / macOS / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001
- Encryption, MFA, audit logs
Integrations & Ecosystem
- SIEM and SOAR tools
- Trend Micro security suite
- API access
Support & Community
- Extensive documentation, training, and support
#7 — Bitdefender GravityZone
Short description: Enterprise EDR with AI detection, centralized management, and advanced threat prevention.
Key Features
- Machine learning and behavioral analytics
- Centralized console
- Anti-ransomware and exploit mitigation
- Automated remediation
- Lightweight agents
- SIEM and threat intelligence integrations
- Cloud and hybrid options
Pros
- Efficient low-resource agents
- Strong malware detection
- Flexible deployment
Cons
- Limited integrations
- Premium license required for advanced features
- Learning curve for complex setups
Platforms / Deployment
- Windows / macOS / Linux / iOS / Android
- Cloud / Hybrid
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM connectors
- API automation
- Threat intelligence feeds
Support & Community
- Documentation and standard support
#8 — VMware Carbon Black
Short description: Cloud-native EDR with behavioral threat detection and automated response for enterprises.
Key Features
- Behavioral analytics and AI detection
- Threat hunting and forensics
- Endpoint isolation and remediation
- SIEM and SOAR integration
- Lightweight agents
- Real-time telemetry
- Automated alert prioritization
Pros
- Strong behavioral detection
- Centralized enterprise visibility
- Integration-friendly
Cons
- Requires skilled teams
- Premium pricing
- Some features complex to configure
Platforms / Deployment
- Windows / macOS / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001
- MFA, encryption, audit logs
Integrations & Ecosystem
- SIEM tools
- SOAR platforms
- APIs for automation
Support & Community
- Documentation, training, enterprise support
#9 — Kaspersky EDR
Short description: Malware-focused EDR with centralized management, suitable for SMB and mid-market organizations.
Key Features
- Threat detection and prevention
- Forensic investigation tools
- Automated response workflows
- Cloud console and reporting
- Lightweight agents
- Integration with Kaspersky suite
- API access
Pros
- Effective malware protection
- Easy deployment
- Affordable for SMBs
Cons
- Limited advanced automation
- Fewer third-party integrations
- Enterprise features limited in SMB versions
Platforms / Deployment
- Windows / macOS / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, GDPR
- MFA, encryption
Integrations & Ecosystem
- SIEM connectors
- Kaspersky suite
- API-based integration
Support & Community
- Standard documentation and support
#10 — McAfee MVISION EDR
Short description: Enterprise EDR with threat analytics, AI-driven detection, and automated response.
Key Features
- AI and machine learning detection
- Threat hunting and behavioral analysis
- Automated remediation
- Centralized dashboard
- Lightweight cross-platform agents
- Cloud reporting and analytics
- SIEM and security stack integration
Pros
- Enterprise-grade analytics
- Strong automation
- Scalable deployments
Cons
- Complex setup
- Premium pricing
- Some integrations need configuration
Platforms / Deployment
- Windows / macOS / Linux / iOS / Android
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001
- MFA, encryption, audit logs
Integrations & Ecosystem
- SIEM platforms
- SOAR tools
- API automation
Support & Community
- Enterprise-level support, documentation, training
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| CrowdStrike Falcon | Enterprise / Hybrid | Windows, macOS, Linux, iOS, Android | Cloud | AI-driven detection & response | N/A |
| SentinelOne Singularity | Enterprise / Mid-market | Windows, macOS, Linux, iOS, Android | Cloud / Hybrid | Autonomous AI remediation | N/A |
| Microsoft Defender | Enterprise | Windows, macOS, Linux, iOS, Android | Cloud / Hybrid | Deep Windows integration | N/A |
| CrowdStrike Falcon Pro | SMB | Windows, macOS, Linux | Cloud | Simplified cloud-native EDR | N/A |
| Sophos Intercept X | SMB / Enterprise | Windows, macOS, Linux | Cloud / Hybrid | Ransomware rollback | N/A |
| Trend Micro Apex One | Enterprise | Windows, macOS, Linux | Cloud / Hybrid | Behavioral & ML detection | N/A |
| Bitdefender GravityZone | Enterprise | Windows, macOS, Linux, iOS, Android | Cloud / Hybrid | Lightweight AI-driven agents | N/A |
| VMware Carbon Black | Enterprise | Windows, macOS, Linux | Cloud / Hybrid | Behavioral analytics | N/A |
| Kaspersky EDR | SMB / Mid-market | Windows, macOS, Linux | Cloud / Hybrid | Centralized threat management | N/A |
| McAfee MVISION EDR | Enterprise | Windows, macOS, Linux, iOS, Android | Cloud / Hybrid | AI-based threat analytics | N/A |
Evaluation & Scoring of Endpoint Detection & Response (EDR)
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| CrowdStrike Falcon | 9 | 8 | 8 | 9 | 9 | 8 | 7 | 8.7 |
| SentinelOne Singularity | 9 | 7 | 7 | 8 | 9 | 7 | 7 | 8.3 |
| Microsoft Defender | 8 | 8 | 7 | 8 | 8 | 8 | 8 | 8.0 |
| CrowdStrike Falcon Pro | 7 | 9 | 6 | 7 | 8 | 7 | 8 | 7.7 |
| Sophos Intercept X | 8 | 8 | 7 | 8 | 8 | 8 | 7 | 7.9 |
| Trend Micro Apex One | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.7 |
| Bitdefender GravityZone | 8 | 7 | 6 | 7 | 8 | 7 | 7 | 7.5 |
| VMware Carbon Black | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.7 |
| Kaspersky EDR | 7 | 8 | 6 | 7 | 8 | 7 | 7 | 7.4 |
| McAfee MVISION EDR | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.7 |
Interpretation: Scores reflect comparative evaluation across features, usability, integration, and value. Weighted totals help organizations prioritize tools based on strategic requirements.
Which Endpoint Detection & Response (EDR) Tool Is Right for You?
Solo / Freelancer
Choose lightweight, cloud-based EDR with minimal management overhead, such as CrowdStrike Falcon Pro or Kaspersky EDR.
SMB
Select solutions with simplified deployment, ransomware protection, and cloud management: Sophos Intercept X, CrowdStrike Falcon Pro, Trend Micro Apex One.
Mid-Market
Scalable EDR with AI threat detection and integration with existing security stack: SentinelOne Singularity, Microsoft Defender, Trend Micro Apex One.
Enterprise
Feature-rich EDR for hybrid deployments, threat hunting, and automated response: CrowdStrike Falcon, VMware Carbon Black, McAfee MVISION EDR.
Budget vs Premium
Budget-focused organizations prioritize lightweight agents and cloud deployment; premium tiers deliver AI, automation, and enterprise integrations.
Feature Depth vs Ease of Use
SMBs may prefer simple dashboards and automated remediation; enterprises benefit from deep analytics and advanced playbooks.
Integrations & Scalability
Ensure compatibility with SIEM, SOAR, IAM, and cloud platforms. Verify agent performance scales with workforce size.
Security & Compliance Needs
Select solutions with SOC 2, ISO 27001, and GDPR compliance if regulatory adherence is critical. MFA, RBAC, and encryption are essential.
Frequently Asked Questions (FAQs)
What pricing models are common for EDR tools?
Most use subscription-based pricing, often per endpoint or user. Enterprise tiers may include threat hunting and advanced analytics.
How long does deployment typically take?
Cloud-native EDR can be deployed in hours to days; hybrid or on-premises setups may require weeks.
Are these tools suitable for remote workforces?
Yes, modern EDR solutions offer cloud agents optimized for remote endpoints and centralized management.
Can EDR replace antivirus software?
EDR enhances antivirus capabilities but may not fully replace them. Many platforms integrate both functions.
How do EDR tools integrate with SIEM or SOAR?
They offer APIs and connectors to centralize alerts, automate responses, and correlate threat intelligence.
What are common implementation mistakes?
Skipping full agent coverage, ignoring SIEM integration, and underestimating alert tuning.
How scalable are these solutions?
Cloud-native platforms scale effortlessly; hybrid/on-prem deployments need planning for agents and telemetry.
How do I switch EDR providers?
Plan migration to ensure full endpoint coverage, preserve threat history, and test automated workflows.
Are these tools suitable for small businesses?
Yes, some platforms offer SMB-focused versions with simplified management and cloud deployment.
Can EDR help with compliance?
Yes, EDR supports regulatory requirements such as GDPR, SOC 2, and HIPAA by providing visibility, audit logs, and automated remediation.
Conclusion
Endpoint Detection & Response tools are essential for modern cybersecurity, providing proactive monitoring, AI-driven detection, and automated remediation across endpoints. Choosing the right EDR depends on organization size, security needs, deployment preferences, and integration requirements. For SMBs, simplified cloud-native options suffice, while enterprises benefit from full-featured platforms with threat hunting and advanced automation. Start by shortlisting 2–3 tools, validate their integrations, and run a pilot to assess performance and ease of use before scaling organization-wide.