Introduction
Deception Technology Tools are advanced cybersecurity solutions that use decoys, traps, and fake assets to detect, mislead, and analyze attackers inside a network. Instead of only blocking threats, these tools proactively lure attackers into interacting with deceptive systems—such as fake credentials, servers, databases, or endpoints—allowing security teams to detect malicious activity early and respond effectively.
Unlike traditional security approaches that rely on signatures or perimeter defenses, deception technology focuses on post-breach detection. It assumes that attackers may eventually bypass defenses and provides a way to catch them quickly before they cause damage. This approach is especially valuable in modern environments where threats are sophisticated and persistent.
Common Use Cases
- Detecting lateral movement inside networks
- Identifying insider threats and compromised accounts
- Protecting critical infrastructure and sensitive data
- Enhancing threat intelligence and attacker behavior analysis
- Reducing dwell time of attackers in networks
What Buyers Should Evaluate
- Ease of deployment and automation of decoys
- Coverage across endpoints, servers, and cloud environments
- Integration with SIEM, SOAR, and security tools
- Real-time alerting and response capabilities
- Accuracy and low false-positive rates
- Scalability across enterprise environments
- Support for identity-based deception techniques
- Threat intelligence and analytics capabilities
- Cost vs operational value
Best for: Enterprises, SOC teams, threat hunters, and organizations seeking advanced threat detection beyond traditional defenses.
Not ideal for: Small teams with basic security needs or environments lacking security monitoring infrastructure.
Key Trends in Deception Technology Tools
- Integration with Extended Detection and Response (XDR)
- AI-driven deception deployment and automation
- Identity-based deception (fake credentials, AD traps)
- Cloud and hybrid environment coverage
- Behavioral analytics for attacker detection
- Integration with SOAR platforms for automated response
- Expansion into IoT and OT environments
- Real-time threat intelligence enrichment
- Low-interaction and high-interaction deception techniques
- Focus on reducing attacker dwell time
How We Selected These Tools (Methodology)
- Strong market adoption and innovation in deception technology
- Proven effectiveness in detecting advanced threats
- Coverage across network, endpoint, and identity layers
- Integration with security ecosystems (SIEM, SOAR, XDR)
- Availability of automation and scalability features
- Suitability for enterprise and mid-market environments
- Strong documentation and support ecosystems
- Balance between specialized and integrated solutions
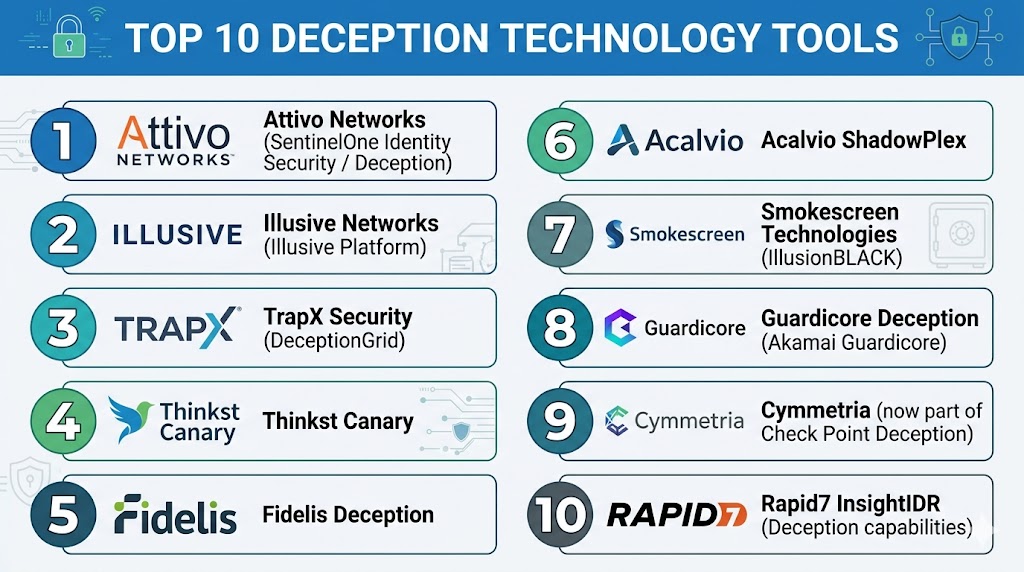
Top 10 Deception Technology Tools
#1 — Attivo Networks (SentinelOne Deception)
Short description: A comprehensive deception platform focusing on identity and endpoint-based deception techniques.
Key Features
- Identity deception
- Endpoint traps
- Threat detection
- Risk analytics
- Integration with security tools
Pros
- Strong identity-focused deception
- Enterprise-ready
Cons
- Complex setup
- Premium pricing
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- RBAC, encryption
- Compliance support varies
Integrations & Ecosystem
- SIEM tools
- APIs
- Security platforms
Support & Community
Enterprise-grade support.
#2 — Illusive Platform (Illusive Networks)
Short description: A deception platform focused on identity-based attack detection and lateral movement prevention.
Key Features
- Identity deception
- Lateral movement detection
- Risk analysis
- Continuous monitoring
- Integration with security tools
Pros
- Strong identity protection
- Low false positives
Cons
- Complex deployment
- Requires expertise
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- Security tools
Support & Community
Enterprise support.
#3 — TrapX DeceptionGrid
Short description: A deception platform that deploys decoys across networks to detect and analyze attackers.
Key Features
- Automated decoy deployment
- Threat detection
- Malware analysis
- Risk assessment
- Integration with SIEM
Pros
- Easy deployment
- Strong detection
Cons
- Limited customization
- Smaller ecosystem
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM tools
- APIs
Support & Community
Good support.
#4 — Thinkst Canary
Short description: A simple and effective deception solution using lightweight decoy devices.
Key Features
- Canary tokens
- Decoy systems
- Real-time alerts
- Easy deployment
- Low maintenance
Pros
- Extremely easy to deploy
- Low cost
Cons
- Limited advanced features
- Not enterprise-grade
Platforms / Deployment
- Cloud / On-prem
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- Alerting tools
Support & Community
Strong community support.
#5 — Fidelis Deception
Short description: A deception platform integrated with broader threat detection and response capabilities.
Key Features
- Network deception
- Threat detection
- Risk analysis
- Integration with XDR
- Automated response
Pros
- Strong integration
- Enterprise capabilities
Cons
- Complex setup
- Requires expertise
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- XDR platforms
- APIs
Support & Community
Enterprise support.
#6 — Acalvio ShadowPlex
Short description: A deception platform focused on automated deployment and threat detection.
Key Features
- Automated deception
- Threat detection
- Risk analytics
- Integration with security tools
- Continuous monitoring
Pros
- Easy deployment
- Strong automation
Cons
- Limited advanced customization
- Growing ecosystem
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- Security tools
Support & Community
Good support.
#7 — Smokescreen IllusionBLACK
Short description: A deception platform focused on endpoint and identity-based threat detection.
Key Features
- Endpoint deception
- Identity traps
- Threat detection
- Risk analysis
- Integration with SIEM
Pros
- Strong endpoint focus
- Real-time detection
Cons
- Requires setup
- Limited ecosystem
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- SIEM tools
Support & Community
Good support.
#8 — Guardicore Deception (Akamai Guardicore)
Short description: A network-focused deception solution integrated into microsegmentation platforms.
Key Features
- Network deception
- Threat detection
- Microsegmentation integration
- Risk analysis
- Real-time alerts
Pros
- Strong network security
- Integrated platform
Cons
- Requires ecosystem adoption
- Complex setup
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- Security tools
Support & Community
Enterprise support.
#9 — Cymmetria (Check Point Deception)
Short description: A deception technology platform focusing on advanced threat detection.
Key Features
- Deception deployment
- Threat detection
- Risk analysis
- Integration with Check Point tools
- Continuous monitoring
Pros
- Strong detection capabilities
- Enterprise-ready
Cons
- Requires ecosystem adoption
- Complex setup
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Check Point ecosystem
- APIs
Support & Community
Enterprise support.
#10 — Rapid7 InsightIDR (Deception Capabilities)
Short description: A security analytics platform with integrated deception features.
Key Features
- Deception techniques
- Threat detection
- SIEM integration
- Risk analysis
- Automated response
Pros
- Integrated platform
- Easy to use
Cons
- Limited standalone deception features
- Requires broader platform
Platforms / Deployment
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM
- APIs
- Security tools
Support & Community
Strong support and documentation.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Attivo | Enterprise | Web | Hybrid | Identity deception | N/A |
| Illusive | Identity security | Web | Cloud | Lateral movement detection | N/A |
| TrapX | SMB/Enterprise | Web | Hybrid | Decoy automation | N/A |
| Thinkst Canary | SMB | Web | On-prem | Simple deployment | N/A |
| Fidelis | Enterprise | Web | Cloud | XDR integration | N/A |
| Acalvio | Automation | Web | Cloud | Automated deployment | N/A |
| Smokescreen | Endpoint | Web | Cloud | Endpoint deception | N/A |
| Guardicore | Network | Web | Cloud | Microsegmentation | N/A |
| Cymmetria | Enterprise | Web | Cloud | Advanced detection | N/A |
| Rapid7 | SIEM users | Web | Cloud | Integrated platform | N/A |
Evaluation & Scoring of Deception Technology Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Attivo | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.5 |
| Illusive | 9 | 7 | 8 | 9 | 9 | 8 | 7 | 8.4 |
| TrapX | 8 | 8 | 7 | 8 | 8 | 7 | 8 | 7.9 |
| Thinkst | 7 | 9 | 6 | 7 | 7 | 7 | 9 | 7.6 |
| Fidelis | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.9 |
| Acalvio | 8 | 8 | 7 | 8 | 8 | 7 | 8 | 7.9 |
| Smokescreen | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.6 |
| Guardicore | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.9 |
| Cymmetria | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.9 |
| Rapid7 | 7 | 8 | 8 | 7 | 7 | 8 | 8 | 7.8 |
How to interpret scores:
- Scores are comparative across tools
- Higher scores indicate stronger overall capabilities
- Enterprise tools excel in integration and depth
- Lightweight tools score higher in ease of use
- Choose based on your threat detection needs
Which Deception Technology Tool Is Right for You?
Solo / Freelancer
Use Thinkst Canary for simple deployment and cost-effectiveness.
SMB
Use TrapX or Acalvio for ease of use and automation.
Mid-Market
Use Smokescreen or Guardicore for balanced features.
Enterprise
Use Attivo, Illusive, or Fidelis.
Budget vs Premium
- Budget: Thinkst Canary
- Premium: Attivo, Illusive
Feature Depth vs Ease of Use
- Deep features: Attivo
- Ease of use: Thinkst Canary
Integrations & Scalability
Best: Attivo, Fidelis
Security & Compliance Needs
Best: Illusive, Guardicore
Frequently Asked Questions (FAQs)
1. What is deception technology?
It uses decoys to detect attackers inside networks.
2. Why is it important?
It helps detect threats that bypass traditional defenses.
3. Does it replace traditional security?
No, it complements existing security tools.
4. Is it difficult to deploy?
Some tools are complex; others are easy to deploy.
5. Can it detect insider threats?
Yes, it is effective for insider threat detection.
6. Does it integrate with SIEM?
Yes, most tools integrate with SIEM platforms.
7. Is it suitable for cloud environments?
Yes, modern tools support cloud and hybrid setups.
8. Are these tools expensive?
Pricing varies based on features and scale.
9. Who should use them?
Organizations with advanced security needs.
10. What is the biggest benefit?
Early detection of attackers.
Conclusion
Deception Technology Tools provide a powerful layer of defense by shifting the focus from prevention to detection and response. By deploying decoys and traps throughout the environment, these tools enable organizations to identify attackers early, reduce dwell time, and gain valuable insights into attack behavior. As cyber threats become more sophisticated, relying solely on traditional defenses is no longer enough. Deception technology complements existing security strategies by adding proactive detection capabilities. While enterprise-grade solutions offer deep integration and advanced features, simpler tools can still provide meaningful security benefits. The best approach is to evaluate your threat landscape, shortlist a few solutions, and test how effectively they integrate into your existing security operations.