Introduction
Secure software supply chain attestation tools help organizations verify the integrity, origin, and build process of software artifacts. These tools generate and validate provenance metadata that proves how code was built, by whom, and under what conditions. This is essential for preventing tampering, ensuring trust, and meeting compliance requirements across modern development pipelines.
With increasing attacks targeting software supply chains, organizations are adopting frameworks like SLSA to enforce stronger security guarantees. Attestation tools play a key role by signing artifacts, maintaining transparency logs, and enabling verification before deployment.
Common use cases include securing CI CD pipelines, validating container images, enforcing deployment policies, auditing build processes, and ensuring compliance across software delivery workflows.
What buyers should evaluate:
- Support for SLSA levels and provenance standards
- Signing and verification mechanisms
- Integration with CI CD pipelines
- Transparency logs and auditability
- Policy enforcement capabilities
- Ease of deployment and automation
- Compatibility with container ecosystems
- Security and cryptographic features
- Scalability for enterprise pipelines
- Ecosystem and community support
Best for: DevSecOps teams, platform engineers, security teams, enterprises, and organizations building secure software delivery pipelines.
Not ideal for: Teams without CI CD pipelines or those not handling sensitive or distributed software artifacts.
Key Trends in Secure Software Supply Chain Attestation Tools
- Rapid adoption of SLSA framework for software integrity
- Integration with CI CD and DevOps pipelines
- Use of cryptographic signing and verification
- Growth of transparency logs for auditability
- Policy-driven deployment enforcement
- Increasing focus on zero trust software delivery
- Integration with container and Kubernetes ecosystems
- Automation of provenance generation
- Expansion of open-source security tooling
- Strong emphasis on compliance and governance
How We Selected These Tools
- Adoption in DevSecOps and cloud-native ecosystems
- Support for SLSA and provenance standards
- Strength of signing and verification capabilities
- Integration with CI CD pipelines
- Security and cryptographic features
- Ease of use and automation
- Scalability for enterprise environments
- Ecosystem and community support
- Compatibility with modern infrastructure
- Active development and updates
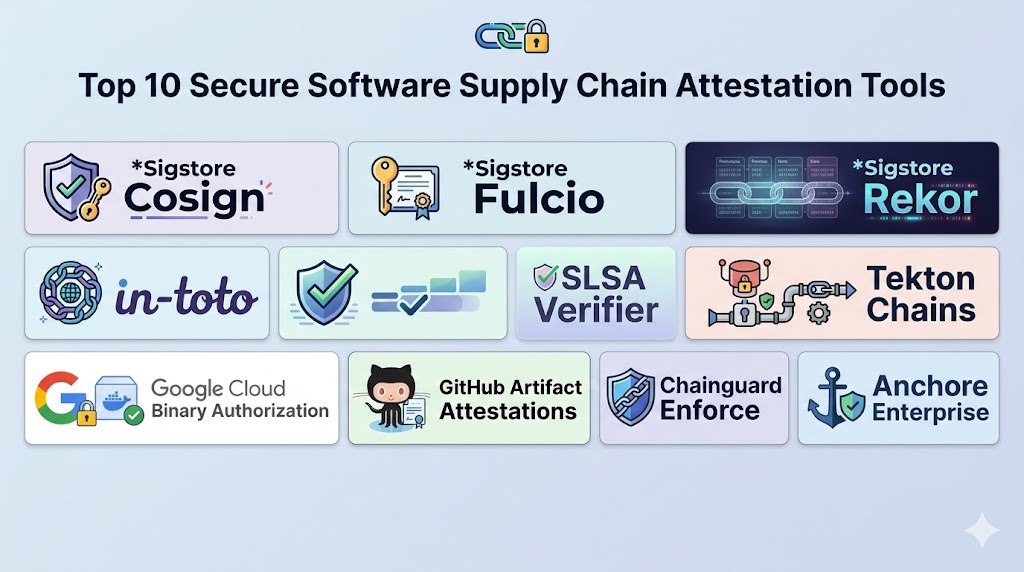
Top 10 Secure Software Supply Chain Attestation Tools
1. Sigstore Cosign
Short description:
Sigstore Cosign is a widely used tool for signing and verifying container images and artifacts. It enables developers to attach cryptographic signatures and provenance data. It is designed for simplicity and security. It is ideal for securing container workflows.
Key Features
- Artifact signing
- Verification tools
- Integration with container registries
- Keyless signing support
- Transparency logs
- Policy enforcement
- CLI tools
Pros
- Easy to use
- Strong security model
- Open-source
Cons
- Requires ecosystem understanding
- Limited UI tools
- Setup complexity
Platforms / Deployment
Linux / Windows / macOS
Deployment: Cloud / Self-hosted
Security & Compliance
Supports cryptographic signing and verification
Integrations & Ecosystem
Cosign integrates with modern DevOps and container workflows.
- Kubernetes
- CI CD pipelines
- Container registries
- DevOps tools
- APIs
- Security systems
Support & Community
Very strong open-source community
2. Sigstore Fulcio
Short description:
Fulcio is a certificate authority that issues short-lived certificates for signing software artifacts. It enables keyless signing workflows. It is part of the Sigstore ecosystem. It is ideal for secure identity-based signing.
Key Features
- Certificate issuance
- Keyless signing
- Identity-based authentication
- Integration with OIDC
- Secure workflows
- Lightweight design
- Open-source
Pros
- Eliminates key management
- Strong identity integration
- Secure design
Cons
- Requires Sigstore ecosystem
- Limited standalone use
- Setup complexity
Platforms / Deployment
Cloud / Self-hosted
Deployment: Hybrid
Security & Compliance
Supports identity-based cryptographic security
Integrations & Ecosystem
Fulcio integrates with Sigstore tools and identity providers.
- OIDC providers
- Cosign
- DevOps pipelines
- APIs
- Security tools
- Cloud platforms
Support & Community
Strong community support
3. Sigstore Rekor
Short description:
Rekor is a transparency log system that records signed metadata for software artifacts. It ensures auditability and integrity of signatures. It is part of the Sigstore ecosystem. It is ideal for compliance and auditing.
Key Features
- Transparency logs
- Immutable records
- Verification support
- Auditability
- Integration with signing tools
- API access
- Open-source
Pros
- Strong audit capabilities
- Immutable logs
- Open ecosystem
Cons
- Requires integration
- Limited standalone functionality
- Setup complexity
Platforms / Deployment
Cloud / Self-hosted
Deployment: Hybrid
Security & Compliance
Provides immutable logging for security verification
Integrations & Ecosystem
Rekor integrates with signing and verification tools.
- Cosign
- Fulcio
- DevOps pipelines
- APIs
- Security tools
- Cloud platforms
Support & Community
Active open-source community
4. in-toto
Short description:
in-toto is a framework for securing software supply chains by tracking steps in the build process. It ensures integrity from source to deployment. It is widely used in security-focused environments. It is ideal for end-to-end provenance tracking.
Key Features
- Supply chain tracking
- Provenance metadata
- Step verification
- Policy enforcement
- Integration with CI CD
- Open-source
- Flexible workflows
Pros
- Strong security model
- Flexible implementation
- Proven framework
Cons
- Complex setup
- Requires expertise
- Limited UI tools
Platforms / Deployment
Cross-platform
Deployment: Self-hosted
Security & Compliance
Supports end-to-end integrity verification
Integrations & Ecosystem
in-toto integrates with build and deployment pipelines.
- CI CD systems
- DevOps tools
- Security frameworks
- APIs
- Build systems
- Automation tools
Support & Community
Strong security community
5. SLSA Verifier
Short description:
SLSA Verifier is a tool for verifying provenance metadata against SLSA standards. It ensures that software meets required security levels. It is designed for compliance validation. It is ideal for enforcing SLSA policies.
Key Features
- Provenance verification
- SLSA compliance checks
- CLI tools
- Integration with pipelines
- Security validation
- Lightweight
- Open-source
Pros
- Focused on SLSA
- Easy to integrate
- Lightweight
Cons
- Limited features
- CLI-based
- Requires SLSA knowledge
Platforms / Deployment
Cross-platform
Deployment: CLI tool
Security & Compliance
Supports SLSA verification
Integrations & Ecosystem
Works with attestation and CI CD tools.
- CI CD pipelines
- DevOps tools
- APIs
- Security tools
- Build systems
- Automation tools
Support & Community
Growing community
6. Tekton Chains
Short description:
Tekton Chains is a Kubernetes-native tool for generating and storing provenance data. It integrates with Tekton pipelines. It automates attestation generation. It is ideal for cloud-native environments.
Key Features
- Provenance generation
- Integration with Tekton
- Kubernetes-native
- Artifact signing
- Transparency logs
- Automation
- Open-source
Pros
- Cloud-native
- Automated workflows
- Strong integration
Cons
- Requires Tekton
- Kubernetes dependency
- Setup complexity
Platforms / Deployment
Kubernetes / Cloud
Deployment: Cloud-native
Security & Compliance
Supports artifact signing and verification
Integrations & Ecosystem
Integrates with Kubernetes and CI CD tools.
- Kubernetes
- Tekton
- DevOps pipelines
- APIs
- Cloud systems
- Security tools
Support & Community
Active community
7. Google Cloud Binary Authorization
Short description:
Binary Authorization enforces deployment policies based on signed artifacts. It ensures only trusted software is deployed. It integrates with Google Cloud environments. It is ideal for enterprise policy enforcement.
Key Features
- Policy enforcement
- Artifact verification
- Integration with GCP
- Access control
- Audit logs
- Security policies
- Deployment controls
Pros
- Strong enforcement
- Enterprise-ready
- Cloud integration
Cons
- Requires GCP
- Complex setup
- Vendor lock-in
Platforms / Deployment
Cloud
Deployment: SaaS
Security & Compliance
Supports policy-based security controls
Integrations & Ecosystem
Integrates with Google Cloud services.
- GCP
- Kubernetes
- DevOps tools
- APIs
- Security systems
- Cloud workflows
Support & Community
Enterprise support
8. GitHub Artifact Attestations
Short description:
GitHub Artifact Attestations provide built-in provenance and signing capabilities within GitHub workflows. It enables developers to secure builds directly in CI pipelines. It is ideal for teams using GitHub.
Key Features
- Artifact attestation
- CI CD integration
- Signing support
- Workflow automation
- Provenance tracking
- GitHub integration
- Security features
Pros
- Easy integration
- Built-in workflow support
- Developer-friendly
Cons
- Limited outside GitHub
- Requires GitHub ecosystem
- Newer feature set
Platforms / Deployment
Cloud
Deployment: SaaS
Security & Compliance
Supports artifact signing and provenance
Integrations & Ecosystem
Integrates with GitHub and DevOps tools.
- GitHub Actions
- CI CD pipelines
- APIs
- Security tools
- Dev workflows
- Cloud platforms
Support & Community
Strong developer community
9. Chainguard Enforce
Short description:
Chainguard Enforce is a policy engine designed to validate software supply chain security. It ensures compliance with provenance and security standards. It is widely used in cloud-native environments. It is ideal for enforcing security policies.
Key Features
- Policy enforcement
- Provenance validation
- Integration with pipelines
- Security controls
- Compliance checks
- Automation
- Cloud-native support
Pros
- Strong enforcement
- Modern design
- Cloud-native
Cons
- Paid solution
- Requires setup
- Smaller ecosystem
Platforms / Deployment
Cloud / Kubernetes
Deployment: SaaS
Security & Compliance
Supports compliance and validation
Integrations & Ecosystem
Integrates with DevOps and cloud systems.
- Kubernetes
- CI CD pipelines
- APIs
- Security tools
- Cloud platforms
- Dev workflows
Support & Community
Growing enterprise support
10. Anchore Enterprise
Short description:
Anchore Enterprise provides software supply chain security with scanning and attestation capabilities. It focuses on container security and compliance. It is ideal for enterprise environments. It supports policy enforcement and verification.
Key Features
- Container scanning
- Attestation support
- Policy enforcement
- Compliance tools
- Integration with pipelines
- Reporting
- Security analysis
Pros
- Enterprise-grade
- Strong security features
- Scalable
Cons
- Paid solution
- Complex setup
- Requires expertise
Platforms / Deployment
Cloud / On-premise
Deployment: Hybrid
Security & Compliance
Supports compliance and policy enforcement
Integrations & Ecosystem
Integrates with enterprise DevOps tools.
- CI CD pipelines
- Kubernetes
- Security tools
- APIs
- Cloud platforms
- Dev workflows
Support & Community
Enterprise-level support
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Cosign | Artifact signing | Multi-platform | Hybrid | Keyless signing | N/A |
| Fulcio | Certificate authority | Cloud | Hybrid | Identity-based signing | N/A |
| Rekor | Transparency logs | Cloud | Hybrid | Immutable logs | N/A |
| in-toto | Supply chain tracking | Cross-platform | Self-hosted | End-to-end integrity | N/A |
| SLSA Verifier | Compliance | Cross-platform | CLI | SLSA validation | N/A |
| Tekton Chains | Cloud-native | Kubernetes | Cloud | Automated provenance | N/A |
| Binary Authorization | Enterprise | Cloud | SaaS | Policy enforcement | N/A |
| GitHub Attestations | CI pipelines | Cloud | SaaS | Built-in workflows | N/A |
| Chainguard | Policy engine | Cloud | SaaS | Security enforcement | N/A |
| Anchore | Enterprise security | Hybrid | Hybrid | Container security | N/A |
Evaluation & Scoring of Secure Software Supply Chain Attestation Tools
| Tool Name | Core | Ease | Integrations | Security | Performance | Support | Value | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Cosign | 9 | 8 | 9 | 10 | 9 | 9 | 9 | 9.2 |
| Fulcio | 8 | 7 | 9 | 10 | 9 | 8 | 9 | 8.8 |
| Rekor | 8 | 7 | 9 | 10 | 9 | 8 | 9 | 8.8 |
| in-toto | 9 | 6 | 8 | 10 | 9 | 9 | 9 | 8.9 |
| SLSA Verifier | 7 | 8 | 8 | 9 | 8 | 7 | 9 | 8.1 |
| Tekton Chains | 9 | 7 | 9 | 9 | 9 | 8 | 8 | 8.8 |
| Binary Authorization | 9 | 7 | 9 | 10 | 9 | 9 | 7 | 8.9 |
| GitHub Attestations | 8 | 9 | 9 | 9 | 8 | 9 | 9 | 8.8 |
| Chainguard | 8 | 7 | 9 | 10 | 9 | 8 | 8 | 8.6 |
| Anchore | 9 | 7 | 9 | 9 | 9 | 9 | 8 | 8.8 |
Scores are comparative and reflect overall capabilities across security, integration, and usability. Higher scores indicate stronger balance, but the right tool depends on your environment and security requirements.
Which Secure Software Supply Chain Tool Is Right for You
Solo / Freelancer
Use Cosign and GitHub Attestations for simple signing and verification workflows.
SMB
Combine Cosign with SLSA Verifier for lightweight compliance.
Mid-Market
Use Tekton Chains and in-toto for scalable pipeline security.
Enterprise
Adopt Binary Authorization, Anchore, or Chainguard for full policy enforcement.
Budget vs Premium
Open-source tools provide strong capabilities, while enterprise tools offer advanced features.
Feature Depth vs Ease of Use
Cosign is simple, while in-toto provides deeper control.
Integrations & Scalability
Tekton and GitHub tools integrate well with pipelines.
Security & Compliance Needs
Choose tools with strong cryptographic and policy features.
Frequently Asked Questions
1. What is software supply chain attestation
It is a process of verifying how software artifacts are built and ensuring their integrity. It provides metadata about the build process. This helps prevent tampering and ensures trust in software delivery.
2. What is SLSA
SLSA is a framework that defines security levels for software supply chains. It helps organizations improve build integrity. It is widely used for secure development practices.
3. Why are attestation tools important
They help verify authenticity and prevent malicious changes. They ensure compliance and improve trust. They are essential for modern DevSecOps.
4. What is provenance
Provenance is metadata that describes how software was built. It includes build steps, tools, and environment. It helps verify integrity.
5. Are these tools only for enterprises
No, they can be used by teams of all sizes. Open-source tools are accessible to smaller teams. Adoption depends on security needs.
6. Do these tools integrate with CI CD
Yes, most tools integrate with CI CD pipelines. This allows automated signing and verification. Integration is a key feature.
7. Are they difficult to implement
Some tools require setup and expertise. Others are easier with built-in integrations. Complexity depends on the tool.
8. Can they prevent attacks
They reduce risk by verifying integrity and enforcing policies. They cannot prevent all attacks. They are part of a broader security strategy.
9. What is keyless signing
It allows signing artifacts without managing private keys. It uses identity-based certificates. It simplifies security workflows.
10. How do I choose the right tool
Identify your pipeline and security needs. Compare features and integrations. Test tools before adoption.
Conclusion
Secure software supply chain attestation tools are becoming essential as organizations face increasing risks from supply chain attacks. These tools provide visibility, integrity, and trust by ensuring that every software artifact can be verified and traced back to its origin. By leveraging frameworks like SLSA and implementing provenance tracking, teams can significantly strengthen their security posture. From lightweight tools like Cosign and SLSA Verifier to enterprise solutions like Binary Authorization and Anchore, the ecosystem offers a wide range of options. Open-source tools provide flexibility and accessibility, while enterprise platforms deliver advanced policy enforcement and compliance capabilities. The right choice depends on your infrastructure, team maturity, and security requirements. There is no single best solution for every organization. A practical approach is to shortlist a few tools, integrate them into your CI CD pipeline, and evaluate their effectiveness. Focus on automation, integration, and scalability to ensure long-term success in securing your software supply chain.