Introduction
Identity & Access Management (IAM) tools are cybersecurity solutions that help organizations manage digital identities and control access to systems, applications, and data. In simple terms, IAM ensures that the right people (or systems) get access to the right resources at the right time—and nothing more.
As businesses move toward cloud environments, remote work, and API-driven systems, IAM has become a foundational layer of security. Without proper identity control, even the most advanced security infrastructure can fail due to unauthorized access or compromised credentials. IAM platforms address this by combining authentication, authorization, and identity lifecycle management into one system.
Real-world use cases include:
- Managing employee access to internal systems and SaaS apps
- Enabling Single Sign-On (SSO) across multiple applications
- Securing APIs and cloud infrastructure
- Enforcing Zero Trust security policies
- Automating user provisioning and de-provisioning
What buyers should evaluate:
- Authentication methods (MFA, biometrics, passwordless)
- Role-based and attribute-based access control
- Integration with cloud and SaaS platforms
- Identity lifecycle management automation
- API and developer support
- Compliance and audit capabilities
- Scalability for large organizations
- Ease of deployment and user experience
- Cost vs value
Best for: Enterprises, IT teams, DevOps engineers, SaaS companies, and organizations managing multiple users, applications, and cloud environments.
Not ideal for: Very small teams with minimal systems or those using basic authentication without complex access requirements.
Key Trends in Identity & Access Management (IAM)
- Rise of Zero Trust security models
- Passwordless authentication adoption
- AI-driven identity risk detection
- Integration with DevSecOps pipelines
- Cloud-native IAM platforms
- API-first identity management
- Identity governance and compliance automation
- Adaptive authentication based on user behavior
- Increased focus on customer identity (CIAM)
- Decentralized identity and digital identity frameworks
How We Selected These Tools (Methodology)
- Evaluated market adoption and vendor reputation
- Assessed authentication and authorization capabilities
- Reviewed security and compliance features
- Analyzed integration with cloud and SaaS ecosystems
- Compared ease of use and deployment flexibility
- Included tools for enterprise and SMB use cases
- Evaluated identity lifecycle management features
- Considered scalability and performance
- Focused on real-world usability and reliability
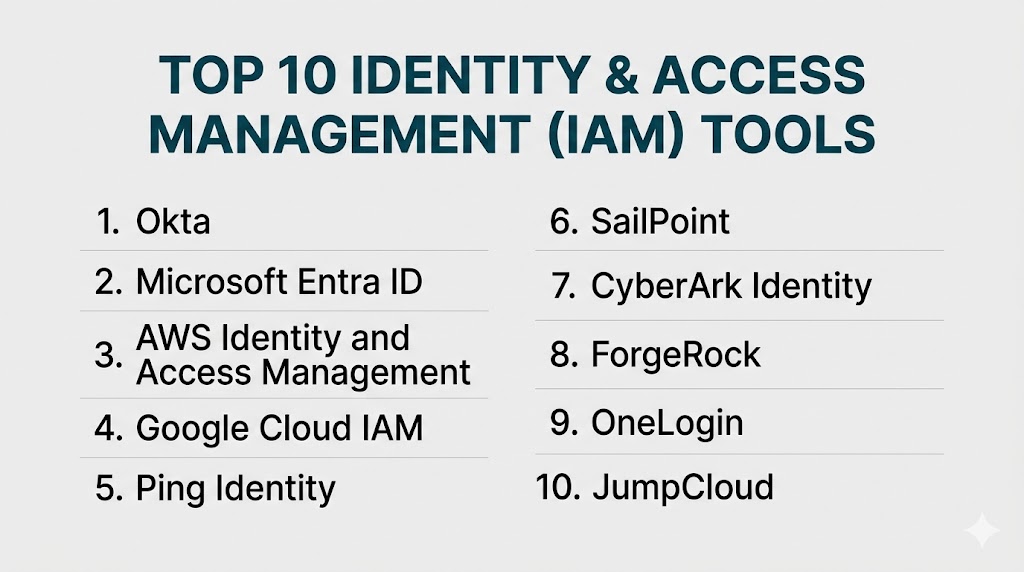
Top 10 Identity & Access Management (IAM) Tools
#1 — Okta
Short description: A leading cloud-based IAM platform offering secure access management for applications, users, and devices.
Key Features
- Single Sign-On (SSO)
- Multi-factor authentication (MFA)
- Lifecycle management
- API access management
- Adaptive authentication
- Directory integration
Pros
- Easy to deploy
- Strong SaaS integrations
Cons
- Premium pricing
- Advanced features require configuration
Platforms / Deployment
Web
Cloud
Security & Compliance
MFA, RBAC, audit logs (certifications not publicly stated)
Integrations & Ecosystem
Okta integrates with thousands of SaaS and enterprise applications.
- Cloud apps
- APIs
- DevOps tools
Support & Community
Strong documentation and large ecosystem.
#2 — Microsoft Entra ID (Azure AD)
Short description: A cloud-based IAM solution integrated with Microsoft ecosystem for identity management and access control.
Key Features
- Single Sign-On
- Multi-factor authentication
- Conditional access policies
- Identity protection
- Directory services
Pros
- Deep Microsoft integration
- Scalable
Cons
- Complex licensing
- Best suited for Microsoft environments
Platforms / Deployment
Web
Cloud
Security & Compliance
MFA, RBAC, encryption (details not publicly stated)
Integrations & Ecosystem
Strong integration with Microsoft ecosystem.
- Office apps
- Azure services
- APIs
Support & Community
Extensive documentation and support.
#3 — AWS IAM
Short description: A cloud-native identity management service for controlling access to AWS resources.
Key Features
- Fine-grained access control
- Role-based permissions
- Policy management
- API security
- Integration with AWS services
Pros
- Seamless AWS integration
- Highly scalable
Cons
- Complex policy structure
- Limited outside AWS
Platforms / Deployment
Web
Cloud
Security & Compliance
IAM policies, encryption (details not publicly stated)
Integrations & Ecosystem
Deep AWS ecosystem integration.
- Cloud services
- APIs
Support & Community
Strong community and documentation.
#4 — Google Cloud IAM
Short description: A cloud IAM service providing fine-grained access control for Google Cloud resources.
Key Features
- Role-based access control
- Policy management
- Integration with Google Cloud
- Identity federation
- Audit logging
Pros
- Strong cloud-native capabilities
- Fine-grained permissions
Cons
- Limited outside Google Cloud
- Requires expertise
Platforms / Deployment
Web
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Integrated with Google Cloud ecosystem.
- APIs
- Cloud services
Support & Community
Strong documentation and support.
#5 — Ping Identity
Short description: An enterprise IAM platform offering identity security and access management solutions.
Key Features
- Single Sign-On
- MFA
- API security
- Identity federation
- Risk-based authentication
Pros
- Strong enterprise features
- Flexible deployment
Cons
- Complex setup
- Premium pricing
Platforms / Deployment
Cloud / On-premises
Hybrid
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Integrates with enterprise and cloud systems.
- APIs
- Security tools
Support & Community
Enterprise-level support.
#6 — ForgeRock
Short description: A comprehensive IAM platform focused on identity lifecycle management and customer identity solutions.
Key Features
- Identity governance
- Access management
- API security
- User lifecycle automation
- Identity federation
Pros
- Highly flexible
- Strong identity governance
Cons
- Complex implementation
- Requires expertise
Platforms / Deployment
Cloud / On-premises
Hybrid
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Supports integration with enterprise ecosystems.
- APIs
- Cloud platforms
Support & Community
Strong enterprise support.
#7 — IBM Security Verify
Short description: An IAM platform providing identity governance, authentication, and access control features.
Key Features
- Single Sign-On
- Multi-factor authentication
- Identity governance
- Risk-based access
- User lifecycle management
Pros
- Strong security features
- Enterprise-ready
Cons
- Complex deployment
- Higher cost
Platforms / Deployment
Cloud / On-premises
Hybrid
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Integrates with enterprise systems.
- APIs
- Security tools
Support & Community
Enterprise support and documentation.
#8 — OneLogin
Short description: A cloud IAM solution focused on simplicity, security, and ease of deployment.
Key Features
- Single Sign-On
- MFA
- Directory integration
- User provisioning
- Access control
Pros
- Easy to use
- Quick deployment
Cons
- Limited advanced features
- Smaller ecosystem
Platforms / Deployment
Web
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Integrates with SaaS applications.
- APIs
- Cloud apps
Support & Community
Good support and documentation.
#9 — SailPoint
Short description: An identity governance platform focused on managing user access and compliance.
Key Features
- Identity governance
- Access certification
- Risk analysis
- Policy management
- Lifecycle automation
Pros
- Strong compliance features
- Advanced governance
Cons
- Complex implementation
- Expensive
Platforms / Deployment
Cloud / On-premises
Hybrid
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Integrates with enterprise systems.
- APIs
- Security platforms
Support & Community
Enterprise-level support.
#10 — CyberArk Identity
Short description: A security-focused IAM solution specializing in privileged access management.
Key Features
- Privileged access control
- MFA
- Risk-based authentication
- Identity lifecycle management
- Session monitoring
Pros
- Strong security focus
- Ideal for privileged access
Cons
- Complex setup
- Premium pricing
Platforms / Deployment
Cloud / On-premises
Hybrid
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Integrates with enterprise security tools.
- APIs
- Security platforms
Support & Community
Strong enterprise support.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Okta | SMB/Enterprise | Web | Cloud | SSO ecosystem | N/A |
| Microsoft Entra ID | Enterprise | Web | Cloud | Microsoft integration | N/A |
| AWS IAM | Cloud users | Web | Cloud | Fine-grained control | N/A |
| Google Cloud IAM | Cloud users | Web | Cloud | Role-based access | N/A |
| Ping Identity | Enterprise | Hybrid | Hybrid | Identity federation | N/A |
| ForgeRock | Enterprise | Hybrid | Hybrid | Identity governance | N/A |
| IBM Verify | Enterprise | Hybrid | Hybrid | Risk-based access | N/A |
| OneLogin | SMB | Web | Cloud | Ease of use | N/A |
| SailPoint | Enterprise | Hybrid | Hybrid | Governance | N/A |
| CyberArk Identity | Enterprise | Hybrid | Hybrid | Privileged access | N/A |
Evaluation & Scoring of IAM Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Okta | 9 | 9 | 9 | 8 | 8 | 8 | 7 | 8.4 |
| Microsoft Entra ID | 9 | 8 | 9 | 9 | 8 | 8 | 8 | 8.6 |
| AWS IAM | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.3 |
| Google IAM | 8 | 7 | 9 | 8 | 8 | 8 | 7 | 7.9 |
| Ping Identity | 9 | 6 | 8 | 9 | 8 | 8 | 6 | 8.0 |
| ForgeRock | 9 | 6 | 8 | 9 | 8 | 8 | 6 | 8.0 |
| IBM Verify | 8 | 6 | 8 | 9 | 8 | 8 | 6 | 7.8 |
| OneLogin | 7 | 9 | 7 | 7 | 7 | 7 | 8 | 7.5 |
| SailPoint | 9 | 6 | 8 | 9 | 8 | 8 | 6 | 8.0 |
| CyberArk | 9 | 6 | 8 | 9 | 8 | 8 | 6 | 8.0 |
How to interpret these scores:
These scores are comparative and based on common enterprise and SMB scenarios. Higher scores indicate stronger capabilities, but the right tool depends on your environment. Cloud-native tools excel in scalability, while enterprise platforms offer deeper governance and security controls.
Which IAM Tool Is Right for You?
Solo / Freelancer
Basic authentication tools or built-in cloud IAM solutions are sufficient.
SMB
Okta and OneLogin provide simplicity, scalability, and strong integrations.
Mid-Market
Microsoft Entra ID and AWS IAM offer powerful cloud-native identity control.
Enterprise
Ping Identity, ForgeRock, SailPoint, and CyberArk provide advanced governance and security.
Budget vs Premium
Budget tools focus on basic authentication, while premium tools deliver automation, compliance, and advanced security.
Feature Depth vs Ease of Use
Advanced IAM tools offer deeper control but require expertise, while simpler tools prioritize usability.
Integrations & Scalability
Choose IAM solutions that integrate with your cloud provider and scale with your organization.
Security & Compliance Needs
Highly regulated industries should prioritize tools with strong governance and audit capabilities.
Frequently Asked Questions (FAQs)
1. What is IAM?
IAM is a framework that manages digital identities and controls access to resources.
2. Why is IAM important?
It prevents unauthorized access and ensures secure access to systems and data.
3. What are the core components of IAM?
Authentication, authorization, identity management, and access control.
4. What is Single Sign-On (SSO)?
SSO allows users to access multiple applications with one login.
5. What is Multi-Factor Authentication (MFA)?
A security method requiring multiple verification factors.
6. Can IAM integrate with cloud platforms?
Yes, most modern IAM tools integrate with cloud ecosystems.
7. What is identity lifecycle management?
Managing user identities from creation to deletion.
8. Are IAM tools necessary for small businesses?
Only if they manage multiple systems or sensitive data.
9. What is Zero Trust in IAM?
A security model where no user is trusted by default.
10. How do I choose the right IAM tool?
Evaluate based on security needs, integrations, and scalability.
Conclusion
Identity & Access Management tools are a cornerstone of modern cybersecurity, ensuring that only authorized users can access critical systems and data. As organizations expand across cloud, remote, and hybrid environments, managing identities becomes increasingly complex and essential. While cloud-native IAM platforms provide scalability and ease of use, enterprise-grade solutions offer deeper governance and advanced security capabilities. The best approach is to identify your access control needs, shortlist a few tools, and test them in your environment to ensure they align with your infrastructure, compliance requirements, and long-term security strategy.