Introduction:
In the current landscape of rapid digital transformation, the safeguarding of containerized environments is regarded as a fundamental necessity rather than a luxury. As organizations transition their mission-critical workloads to Kubernetes, a significant increase in the complexity of security vulnerabilities is observed. It is widely acknowledged that the traditional perimeter-based security models are no longer sufficient for dynamic, ephemeral clusters. Consequently, a shift toward a “security-first” architecture is being implemented by leading tech enterprises worldwide.
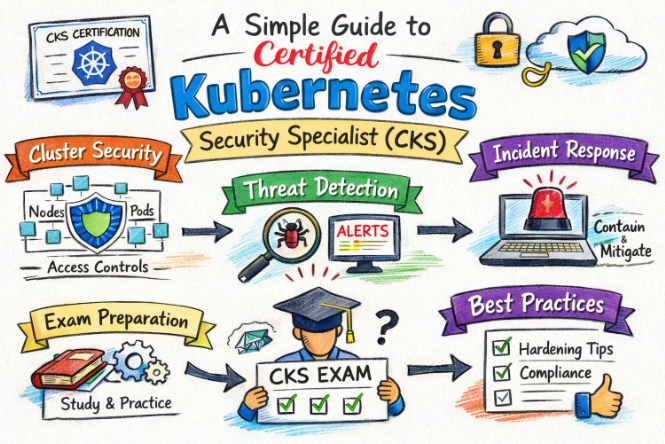
The Certified Kubernetes Security Specialist (CKS) is recognized as the gold standard for professionals who are tasked with protecting these modern infrastructures. This certification is designed to ensure that the entire software supply chain—from the initial code commit to the final runtime execution—is thoroughly hardened against potential threats. For engineers based in India and across the globe, the mastery of these defensive techniques is viewed as a primary differentiator in a competitive job market.
The Strategic Importance of CKS in the Modern Automation Era
The entire cloud and automation ecosystem is now being governed by strict compliance and security protocols. When a cluster is left unsecured, massive financial and reputational losses are often incurred by the business. The CKS curriculum is built to address these specific risks by teaching the implementation of robust security controls. By focusing on the intersection of operations and security, a more resilient infrastructure is created, ensuring that the integrity of data is maintained at all times.
The Value of Professional Validation for Technical Leaders
The importance of formal certifications for both individual contributors and engineering management is frequently discussed in industry circles. By achieving the CKS, a professional’s ability to handle high-stakes security scenarios is verified through a rigorous, hands-on examination. For managers, these credentials are used to build high-performance teams that are capable of meeting global security standards. For engineers, a deeper sense of professional confidence is gained when these complex skills are formally validated.
Why Choose DevOpsSchool?
The decision to partner with DevOpsSchool for certification preparation is often driven by the need for high-quality, practical training. A unique learning methodology is provided, where the focus is placed on solving real-world security puzzles rather than mere rote memorization. The training environment is structured to mirror the challenges faced by top-tier SRE and Security teams.
A wealth of resources, including live mentorship and simulated lab environments, is offered to every learner. This ensures that the intricate details of Kubernetes security are fully grasped before the actual exam is attempted. Furthermore, a community-driven approach is fostered, allowing students to learn from the collective experiences of seasoned industry veterans who have managed large-scale production environments.
Certification Deep-Dive: Certified Kubernetes Security Specialist (CKS)
What is this certification?
A performance-based validation is provided by the CKS, focusing on the security of container-based applications. It is widely considered one of the most advanced technical exams in the cloud-native space.
Who should take this certification?
This program is ideally suited for individuals who already possess a strong foundation in Kubernetes administration. It is highly recommended for Security Architects, Platform Engineers, and DevOps specialists who are responsible for the end-to-end security of cloud workloads.
Detailed Certification Overview Table
| Track | Level | Ideal Candidate | Mandatory Prerequisite | Core Competencies | Sequence |
| DevSecOps | Advanced | Security Practitioners | CKA Credential | Supply Chain & Runtime Security | Post-CKA |
| DevOps | Advanced | Infrastructure Leads | CKA Credential | Policy Management & Hardening | Post-CKA |
| SRE | Specialist | Reliability Experts | CKA Knowledge | Auditing & Threat Detection | Advanced Stage |
| AIOps | Specialist | ML Platform Engineers | Kubernetes Basics | Model & Data Protection | Post-Core |
| DataOps | Specialist | Data Architects | Basic K8s | Encryption & Access Governance | Optional |
| FinOps | Associate | Cloud Economists | Cloud Foundations | Secure Resource Allocation | Foundational |
Skills You Will Gain
- Defensive Cluster Configuration: The underlying infrastructure is hardened by restricting access to the API server and securing the ETCD layer.
- Host-Level Security Hardening: The attack surface is minimized through the use of tools like AppArmor and Seccomp profiles at the OS level.
- Application Isolation: Microservices are isolated using granular Network Policies, ensuring that lateral movement by attackers is prevented.
- Vulnerability Management: Container images are scanned for known vulnerabilities, and only trusted images are allowed to be deployed.
- Continuous Runtime Monitoring: Real-time analysis of system calls and file system changes is performed to detect unauthorized activity.
Real-World Projects Post-Certification
- A fully automated “zero-trust” network architecture is implemented within a production Kubernetes cluster.
- A secure container image registry is established with mandatory vulnerability gates in the CI/CD pipeline.
- Advanced auditing and logging mechanisms are configured to meet strict regulatory compliance requirements.
- Pod Security Admissions are deployed to enforce security best practices across all development teams.
- Runtime security alerts are integrated with centralized incident response systems for immediate mitigation.
Customized Preparation Blueprints
The 7–14 Days Sprint (Intensive Review)
- The primary focus is placed on the official curriculum domains with the highest weightage.
- Documentation for Falco, Trivy, and Kube-bench is thoroughly reviewed for quick reference.
- Short, focused lab sessions are conducted daily to master the YAML syntax for Network Policies.
- One simulated exam is performed under timed conditions to gauge readiness.
The 30 Days Strategic Plan (Structured Learning)
- First Fortnight: Deep dives into cluster setup and system hardening are prioritized.
- Third Week: Supply chain security and microservice isolation techniques are practiced in detail.
- Final Week: Runtime security and auditing are mastered, followed by multiple mock examinations.
The 60 Days Mastery Plan (Comprehensive Depth)
- Month 1: Every domain is explored with an emphasis on the underlying security principles and tools.
- Month 2: Extensive hands-on practice is conducted in diverse lab environments to build muscle memory.
- Conclusion: A final round of intensive review and mock testing is completed to ensure maximum confidence.
Strategic Pitfalls to Avoid
- The CKA prerequisite is undervalued; a strong administrative foundation is required for success.
- Documentation search skills are not sharpened, leading to wasted time during the performance-based exam.
- Complex scenarios are over-analyzed, resulting in unfinished tasks within the two-hour window.
- The importance of context switching between multiple clusters is ignored during preparation.
- Minor configuration errors, such as incorrect namespaces or labels, are not double-checked.
The Path Beyond CKS
- Same-Track Growth: Certified Kubernetes Application Developer (CKAD) for full-stack Kubernetes mastery.
- Cross-Track Exploration: Google Professional Cloud Security Engineer or AWS Security Specialty.
- Leadership Alignment: CISM (Certified Information Security Manager) for those moving into management.
Choose Your Learning Path
The DevOps Trajectory
A focus on the automation of infrastructure security is maintained in this path. The goal is to ensure that security controls do not slow down the speed of delivery.
The DevSecOps Trajectory
This path is chosen by those who wish to become specialized security champions. The “shift-left” philosophy is deeply integrated into every technical process.
The Site Reliability Engineering (SRE) Trajectory
Security is viewed through the lens of system uptime and reliability. Monitoring and rapid incident response are the core pillars of this learning journey.
The AIOps / MLOps Trajectory
The unique security requirements of Artificial Intelligence workloads are addressed here. Protection of data pipelines and model integrity is emphasized.
The DataOps Trajectory
The governance and protection of sensitive data at scale are prioritized. This path is essential for engineers working in highly regulated industries.
The FinOps Trajectory
While the focus remains on cost efficiency, the security implications of resource allocation are studied to prevent “denial-of-wallet” attacks.
Role → Recommended Certifications Mapping
| Professional Role | Primary Recommendation | Secondary Growth Path |
| DevOps Engineer | CKA | CKS |
| Site Reliability Engineer | CKA | CKS |
| Platform Architect | CKS | Vault Operations |
| Cloud Security Engineer | CKS | Cloud-Specific Security |
| Security Consultant | CKS | CISSP Foundations |
| Data Platform Engineer | CKA | CKS |
| FinOps Analyst | FinOps Certified | CKS |
| Engineering Director | CKS | CISM / CISA |
Next Certifications to Take
For the Technical Specialist:
- Same-Track: Certified Kubernetes Application Developer (CKAD).
- Cross-Track: Terraform Associate for infrastructure-as-code security.
- Leadership: PMP for structured project oversight.
For the Security Architect:
- Same-Track: Advanced Vault Management.
- Cross-Track: Azure Security Engineer Associate (AZ-500).
- Leadership: Certified Information Systems Security Professional (CISSP).
Training & Certification Support Institutions
DevOpsSchool
A highly structured approach to CKS training is provided, with a heavy emphasis on hands-on lab exercises. Students are mentored by experts who bring years of production-level Kubernetes experience to the classroom.
Cotocus
A consulting-driven training model is followed at Cotocus, ensuring that learners are exposed to real-world industry problems. The curriculum is designed to bridge the gap between theory and practical implementation.
ScmGalaxy
This platform is recognized as a major hub for community-driven learning and technical resources. A wide array of tutorials and certification guides are made available to the global DevOps community.
BestDevOps
The simplification of complex cloud-native concepts is the primary goal of BestDevOps. Learners are provided with clear, concise paths to master modern automation tools and security practices.
devsecopsschool.com
Advanced security methodologies are the sole focus of this institution. It is considered an essential destination for those who wish to specialize in the “Security” aspect of DevOps.
sreschool.com
The principles of system reliability and security are taught in tandem here. The curriculum is optimized for engineers who are responsible for maintaining high-availability cloud environments.
aiopsschool.com
The emerging field of AI-driven operations is explored through specialized courses. Modern automation and intelligence-gathering techniques are integrated into the training programs.
dataopsschool.com
The lifecycle of data in the cloud is managed through the specialized training offered here. A focus on data security and operational efficiency is maintained throughout the courses.
finopsschool.com
The intersection of cloud finance and technical security is taught at this institution. Strategies for optimizing cloud spend without compromising on security are provided to all students.
General FAQs Section
- Is the CKS exam considered difficult for beginners?
It is generally viewed as an advanced exam, so a strong background in Kubernetes is required before attempting it. - What is the recommended study time?
A period of 6 to 10 weeks of consistent study is usually suggested for most professionals. - Are there any mandatory prerequisites?
A valid CKA certification must be active in the candidate’s profile to be eligible for the CKS. - How is the exam environment structured?
A live, browser-based terminal is provided where various security tasks must be solved within a set time. - Does this certification help in salary negotiations?
Yes, security specialists in the Kubernetes domain are often compensated at a much higher rate. - Can the exam be scheduled at any time?
The exam is available for scheduling online at the candidate’s convenience, subject to proctor availability. - What is the passing threshold for the CKS?
A minimum score of 67% is required to be recognized as a certified specialist. - How long does it take to receive the results?
The results are typically delivered via email within 24 to 36 hours after the exam is completed. - Are specific security tools tested in the exam?
Tools such as Falco, Trivy, and various admission controllers are included in the testing scenarios. - Is the exam available in multiple languages?
The exam is primarily offered in English, though some documentation supports other languages. - How is the identity of the candidate verified?
A government-issued photo ID is checked by the remote proctor before the exam begins. - Is the certification recognized globally?
Yes, it is issued by the Cloud Native Computing Foundation (CNCF) and is recognized by top tech firms worldwide.
CKS Specific FAQs
- Is the API server hardening a major topic?
The configuration of secure flags and authentication for the API server is frequently tested. - How are Network Policies evaluated?
The ability to restrict traffic between specific namespaces and pods is a core part of the examination. - Is secret management included?
The creation and secure handling of Kubernetes secrets, including encryption at rest, are required skills. - Are runtime security alerts monitored during the exam?
The configuration of rules to detect suspicious behavior is often a part of the tasks. - What is the focus on supply chain security?
Vulnerability scanning and the use of authorized image registries are heavily emphasized. - Is knowledge of the Linux kernel required?
A basic understanding of kernel-level security features like AppArmor is necessary for system hardening tasks. - How many clusters are typically used in the exam?
Candidates are often required to work across multiple clusters with different security configurations. - Is the use of “kubectl” commands sufficient?
While “kubectl” is the primary tool, editing configuration files directly on the master and worker nodes is also required.
Testimonials
Aarav
The journey toward the CKS was challenging but incredibly rewarding. A completely new perspective on infrastructure security was gained, and it is now applied to every project at work.
Meera
Confidence in managing large-scale secure clusters was built through the rigorous preparation for this certification. The practical skills learned are used on a daily basis to protect our workloads.
Vikram
Professional growth was noticeably accelerated after the completion of this program. The ability to speak with authority on cloud-native security has opened many new doors in the industry.
Zara
The clarity provided by this roadmap was essential for success. The focus on real-world projects ensured that the skills were not just theoretical but immediately applicable to our production environment.
Ishaan
A significant improvement in technical depth was experienced during the study phase. The integration of security into the DevOps pipeline is now handled with much more precision and ease.
Conclusion: Securing the Future of Cloud Computing
In conclusion, the Certified Kubernetes Security Specialist (CKS) is viewed as a vital milestone for any professional committed to the cloud-native ecosystem. It represents a shift from being a generalist to becoming a specialized guardian of digital assets. By mastering the CKS domains, a more secure and reliable future for software delivery is ensured.
Long-term career success is often found at the intersection of operational excellence and security expertise. Every engineer and manager is encouraged to treat security as a continuous journey rather than a one-time task. Through strategic planning and dedicated learning, the highest standards of infrastructure integrity can be achieved, leading to sustained professional and organizational growth.