Introduction
Software Composition Analysis (SCA) tools are solutions designed to identify, analyze, and manage open-source components within applications. Modern software heavily relies on third-party libraries and dependencies, and SCA tools help teams track these components, detect vulnerabilities, and ensure license compliance.
In today’s development landscape, where applications are built using hundreds of open-source dependencies, SCA tools play a critical role in security and compliance. They enable organizations to adopt a shift-left security approach, catching risks early in the development lifecycle. With increasing regulatory requirements and supply chain attacks, SCA tools have become essential for maintaining secure and compliant software ecosystems.
Real-World Use Cases
- Identifying vulnerable open-source dependencies
- Managing software licenses and compliance
- Monitoring software supply chain risks
- Integrating security checks into CI/CD pipelines
- Generating Software Bill of Materials (SBOM)
What Buyers Should Evaluate
- Depth of vulnerability database coverage
- License compliance management
- Integration with CI/CD and SCM tools
- Real-time monitoring capabilities
- Ease of implementation and configuration
- Reporting and analytics
- Scalability for large applications
- Deployment options (cloud/self-hosted)
Best for: DevSecOps teams, security engineers, compliance teams, and enterprises managing open-source-heavy applications.
Not ideal for: Projects with minimal external dependencies or teams not concerned with compliance or security risks.
Key Trends in Software Composition Analysis (SCA) Tools
- Increased focus on software supply chain security
- Automated SBOM generation and management
- AI-driven vulnerability prioritization
- Integration with DevSecOps pipelines
- Real-time monitoring of dependencies
- Policy-based compliance enforcement
- Expansion of vulnerability databases
- Cloud-native SCA platforms
- Automation of remediation workflows
- Developer-first security tools
How We Selected These Tools (Methodology)
- Strong adoption across DevSecOps environments
- Comprehensive vulnerability and license analysis
- Integration with modern development workflows
- Proven reliability and scalability
- Security and compliance capabilities
- Multi-language and ecosystem support
- Active development and vendor support
- Balance between open-source and enterprise solutions
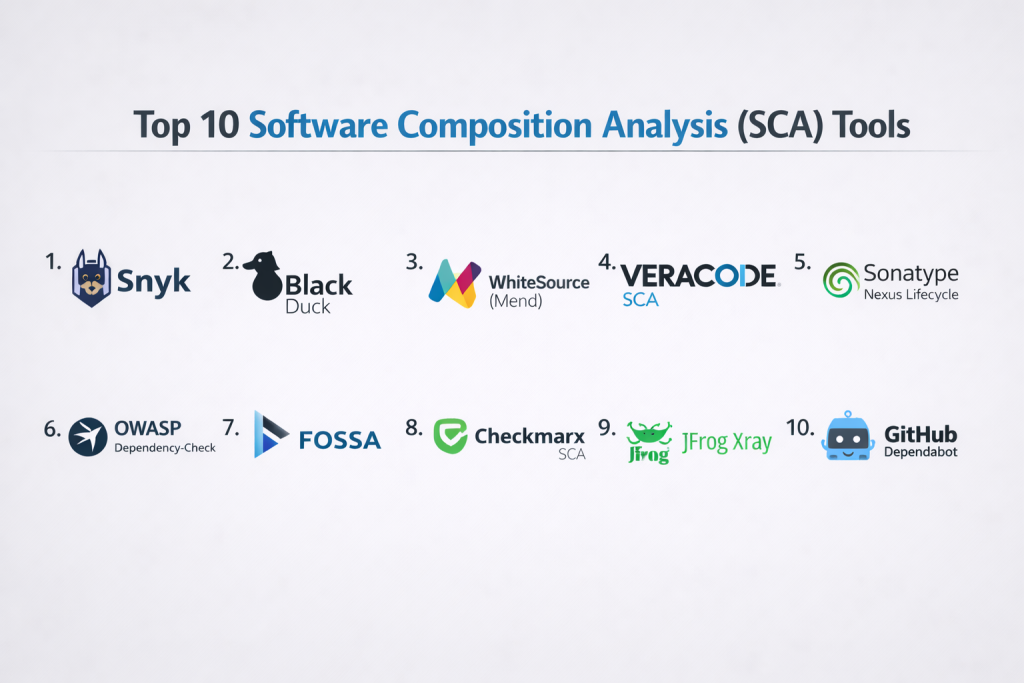
Top 10 Software Composition Analysis (SCA) Tools
#1 — Snyk
Short description: A developer-first security platform focusing on vulnerability detection and remediation for open-source dependencies.
Key Features
- Vulnerability scanning
- Real-time dependency monitoring
- Automated fix suggestions
- CI/CD integration
- Developer-friendly interface
Pros
- Easy to integrate
- Strong developer experience
Cons
- Advanced features require paid plans
- Limited offline capabilities
Platforms / Deployment
Web / IDE plugins
Cloud
Security & Compliance
Security scanning features
Not publicly stated
Integrations & Ecosystem
- GitHub
- GitLab
- Bitbucket
- CI/CD tools
Support & Community
Strong documentation and developer support.
#2 — Black Duck
Short description: An enterprise-grade SCA solution for managing open-source security and compliance risks.
Key Features
- Vulnerability detection
- License compliance management
- Policy enforcement
- Risk reporting
- SBOM generation
Pros
- Comprehensive enterprise features
- Strong compliance capabilities
Cons
- Expensive
- Complex setup
Platforms / Deployment
Web
Cloud / Self-hosted
Security & Compliance
Security and compliance features
Not publicly stated
Integrations & Ecosystem
- DevOps tools
- CI/CD pipelines
Support & Community
Enterprise support available.
#3 — WhiteSource (Mend)
Short description: A widely used SCA tool focusing on open-source security and compliance.
Key Features
- Dependency scanning
- License management
- Automated remediation
- Policy enforcement
- CI/CD integration
Pros
- Strong automation
- Broad language support
Cons
- UI complexity
- Paid plans
Platforms / Deployment
Web
Cloud / Hybrid
Security & Compliance
Security and compliance features
Not publicly stated
Integrations & Ecosystem
- Git platforms
- CI/CD tools
Support & Community
Strong enterprise support.
#4 — Veracode SCA
Short description: A security-focused SCA solution integrated into a broader application security platform.
Key Features
- Vulnerability detection
- Risk prioritization
- Compliance reporting
- Integration with DevSecOps
- Continuous monitoring
Pros
- Strong security capabilities
- Enterprise-grade
Cons
- Expensive
- Complex onboarding
Platforms / Deployment
Web
Cloud
Security & Compliance
Security and compliance features
Not publicly stated
Integrations & Ecosystem
- CI/CD tools
- DevOps platforms
Support & Community
Enterprise support.
#5 — Sonatype Nexus Lifecycle
Short description: A platform for managing open-source risk and enforcing governance policies.
Key Features
- Vulnerability detection
- Policy enforcement
- Dependency tracking
- SBOM support
- CI/CD integration
Pros
- Strong governance features
- Enterprise scalability
Cons
- Complex setup
- Pricing
Platforms / Deployment
Web
Cloud / Self-hosted
Security & Compliance
Security features
Not publicly stated
Integrations & Ecosystem
- Maven
- Jenkins
- CI/CD tools
Support & Community
Enterprise support available.
#6 — OWASP Dependency-Check
Short description: An open-source tool for identifying vulnerable dependencies.
Key Features
- Vulnerability database scanning
- Open-source
- CI/CD integration
- Reporting
- Multi-language support
Pros
- Free to use
- Easy integration
Cons
- Limited advanced features
- Manual configuration required
Platforms / Deployment
Windows / macOS / Linux
Local / CI integration
Security & Compliance
Basic vulnerability detection
Not publicly stated
Integrations & Ecosystem
- Build tools
- CI/CD pipelines
Support & Community
Active open-source community.
#7 — FOSSA
Short description: A compliance-focused SCA tool for managing open-source licenses and risks.
Key Features
- License compliance tracking
- Dependency analysis
- Risk management
- SBOM generation
- CI/CD integration
Pros
- Strong compliance focus
- Easy to use
Cons
- Limited deep security analysis
- Paid plans
Platforms / Deployment
Web
Cloud
Security & Compliance
Compliance features
Not publicly stated
Integrations & Ecosystem
- Git platforms
- CI/CD tools
Support & Community
Good documentation.
#8 — Checkmarx SCA
Short description: A security-focused SCA tool integrated into a broader application security platform.
Key Features
- Vulnerability detection
- Risk analysis
- Policy enforcement
- CI/CD integration
- Reporting
Pros
- Strong security capabilities
- Enterprise-ready
Cons
- Complex setup
- Cost
Platforms / Deployment
Web
Cloud / Self-hosted
Security & Compliance
Security features
Not publicly stated
Integrations & Ecosystem
- DevOps tools
- CI/CD pipelines
Support & Community
Enterprise support.
#9 — JFrog Xray
Short description: A security and compliance tool integrated with artifact repositories.
Key Features
- Vulnerability scanning
- License compliance
- Policy enforcement
- Artifact analysis
- CI/CD integration
Pros
- Strong integration with artifact management
- Real-time scanning
Cons
- Requires JFrog ecosystem
- Pricing
Platforms / Deployment
Web
Cloud / Self-hosted
Security & Compliance
Security features
Not publicly stated
Integrations & Ecosystem
- JFrog Artifactory
- CI/CD tools
Support & Community
Enterprise support.
#10 — GitHub Dependabot
Short description: A tool for automated dependency updates and vulnerability alerts within GitHub repositories.
Key Features
- Automated dependency updates
- Vulnerability alerts
- Integration with repositories
- Pull request automation
- Security monitoring
Pros
- Easy to use
- Integrated with GitHub
Cons
- Limited outside GitHub
- Basic features
Platforms / Deployment
Web
Cloud
Security & Compliance
Security alert features
Not publicly stated
Integrations & Ecosystem
- GitHub repositories
- CI/CD tools
Support & Community
Strong GitHub ecosystem support.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Snyk | Dev teams | Web | Cloud | Developer-first | N/A |
| Black Duck | Enterprise | Web | Hybrid | Compliance | N/A |
| Mend | SMB/Enterprise | Web | Hybrid | Automation | N/A |
| Veracode SCA | Security teams | Web | Cloud | Risk analysis | N/A |
| Nexus Lifecycle | Enterprises | Web | Hybrid | Governance | N/A |
| OWASP DC | Open-source | Multi-OS | Local | Free | N/A |
| FOSSA | Compliance | Web | Cloud | License tracking | N/A |
| Checkmarx | Security | Web | Hybrid | Risk analysis | N/A |
| JFrog Xray | DevOps | Web | Hybrid | Artifact scanning | N/A |
| Dependabot | GitHub users | Web | Cloud | Auto updates | N/A |
Evaluation & Scoring of Software Composition Analysis (SCA) Tools
| Tool Name | Core | Ease | Integrations | Security | Performance | Support | Value | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Snyk | 9 | 9 | 9 | 9 | 8 | 9 | 8 | 8.9 |
| Black Duck | 10 | 7 | 8 | 10 | 9 | 9 | 6 | 8.8 |
| Mend | 9 | 8 | 9 | 9 | 8 | 8 | 7 | 8.4 |
| Veracode | 9 | 7 | 8 | 10 | 9 | 9 | 6 | 8.6 |
| Nexus | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.5 |
| OWASP DC | 7 | 7 | 7 | 7 | 7 | 7 | 10 | 7.6 |
| FOSSA | 8 | 8 | 8 | 7 | 8 | 8 | 8 | 8.0 |
| Checkmarx | 9 | 7 | 8 | 9 | 9 | 8 | 6 | 8.3 |
| JFrog Xray | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.4 |
| Dependabot | 8 | 9 | 8 | 8 | 8 | 8 | 9 | 8.3 |
How to interpret scores:
These scores provide a comparative overview of each tool’s strengths. Higher scores indicate better balance across features and usability, but the best choice depends on your priorities. Enterprise tools excel in security and compliance, while lightweight tools offer better value and ease of use.
Which Software Composition Analysis (SCA) Tools Tool Is Right for You?
Solo / Freelancer
Dependabot and OWASP Dependency-Check are simple and cost-effective.
SMB
Snyk and Codacy-like tools provide automation and ease of use.
Mid-Market
Mend and Sonatype Nexus Lifecycle offer scalability and governance.
Enterprise
Black Duck, Veracode, and Checkmarx provide strong compliance and security.
Budget vs Premium
- Budget: OWASP Dependency-Check
- Premium: Black Duck, Veracode
Feature Depth vs Ease of Use
- Feature-rich: Black Duck
- Easy-to-use: Snyk
Integrations & Scalability
- Best integrations: Snyk
- Scalable: Nexus Lifecycle
Security & Compliance Needs
- Strong security: Veracode, Black Duck
- Moderate: FOSSA
Frequently Asked Questions (FAQs)
What is SCA?
It analyzes open-source dependencies for vulnerabilities and compliance issues.
Why is SCA important?
It helps secure the software supply chain.
Are SCA tools automated?
Yes, most provide automated scanning.
Do they support CI/CD?
Yes, integration is a core feature.
Are SCA tools free?
Some offer free tiers; others are paid.
Can they detect license issues?
Yes, many tools include compliance checks.
What is SBOM?
A list of all components used in software.
Can small teams use SCA tools?
Yes, especially lightweight tools.
Do they detect vulnerabilities in real time?
Many modern tools do.
What is the best SCA tool?
Depends on your needs—Snyk is widely used.
Conclusion
Software Composition Analysis tools are essential for managing the growing complexity of open-source dependencies in modern applications. From developer-friendly platforms like Snyk to enterprise-grade solutions like Black Duck and Veracode, each tool offers unique strengths in security, compliance, and automation. As software supply chain risks continue to rise, adopting the right SCA tool is critical for maintaining secure and compliant applications. The best approach is to shortlist a few tools, integrate them into your CI/CD pipeline, and evaluate how effectively they identify and mitigate risks in your development workflow.